Hello everyone, I'm Faiz — security researcher and bug bounty hunter. This is the first article in an ongoing series about how I started bug bounty and how you can get started too.
Let me be honest with you. When I first heard about bug bounty, I thought — okay, people find bugs, companies pay them. How hard can it be?
But it turns out to be very hard.
I started on HackerOne like most people do. Made an account, picked a program, opened Burp Suite, and just… stared. Spent weeks trying to find something — anything — and got nothing. Not even a duplicate. Just silence.
At that point I genuinely thought about giving it up. Maybe this was only for people who already had years of experience. Maybe I was too late.
The Google dork rabbit hole
Someone on Reddit mentioned Hall of Fame programs — companies that don't pay money but publicly recognise you for finding bugs. Lower pressure, real targets, real bugs. Perfect place to practice.
That's when I found this dork list by sushiwushi:
inurl:responsible disclosure hall of fame
I also used the full dork list at github.com/sushiwushi/bug-bounty-dorks — bookmark it if you're starting out.
Pro tip: Modify the dorks using AI to get better results.
One target kept coming up lets say redacted.com. I ran it through Wappalyzer and saw it was built on WordPress. That immediately triggered a checklist in my head.
My WordPress hunting steps — click each to expand
1.Fingerprint the tech stack with Wappalyzer
2.Pull up a WordPress-specific checklist. I use https://github.com/0xmaximus/Galaxy-Bugbounty-Checklist/blob/main/WordPress/README.md
3.Test the WordPress REST API user endpoint
4.Document and report responsibly
What I found — a live PII disclosure
I visited the endpoint and immediately saw something I wasn't supposed to see. Real employee names and usernames exposed to the entire internet. This is called PII disclosure — Personally Identifiable Information exposed without any login required.
The report I sent
Excerpt from my report:
Using the REST API, an attacker can enumerate WordPress users and their personal information. The endpoint at /wp-json/wp/v2/users is publicly accessible and exposes real employee names and usernames — which can be leveraged in targeted brute force attacks against the login panel. References: HackerOne #356047, #370777.
I sent it with screenshots, steps to reproduce, and the impact section. Then I waited.
A few days later they responded — they acknowledged the bug, fixed it, and added me to their Security Hall of Fame.
I'm not going to lie — I refreshed that page about ten times.
What this actually taught me
That first Hall of Fame didn't pay anything. But it gave me something more important — proof that I could find real bugs on real production systems. Not just labs, not just CTFs.
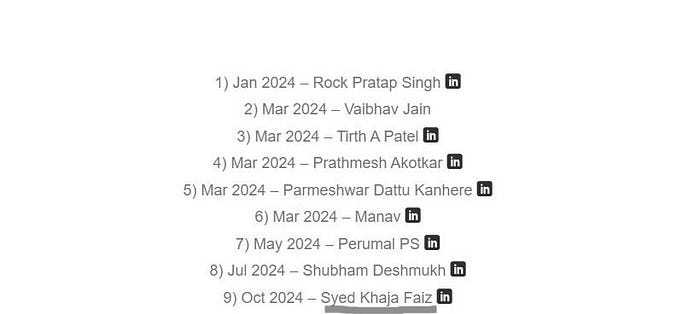
After that I kept going. More Hall of Fame recognitions, slowly built my methodology, then moved to programs that actually pay. That's when things got interesting — and I'll share those stories in the next articles. But if you're reading this at that "HackerOne is giving me nothing" stage — don't quit. Step back. Hunt Hall of Fame targets. Use dorks. Build your process. The skills compound.
Money follows skill. Focus on the skill first.
This is my first Medium article. If it helped you, follow along — more writeups coming soon and feel free to connect on linkedin https://www.linkedin.com/in/khajafaiz/