1. Entry Point: Phone Verification (KYC) Bypass
The application enforces a mandatory phone verification step after registration at a specific gate. However, this was implemented as a weak client-side redirect.
- Vulnerability: Broken Access Control / Bypass.
- Methodology:
- Register a new account.
- Intercept the redirect to the verification endpoint.
https://test.com/public/kyc-approval?customerId=X&redirect_uri=/public/profile
- Manually modify the URL to the user profile path and stop the page load before the redirect triggers.
https://test.com/public/profile
To make it persistent, I used Burp's rule to automatically swap the verification URL with the profile URL in every outgoing request.
- Result: Full access to the authenticated user dashboard without completing the required KYC process.
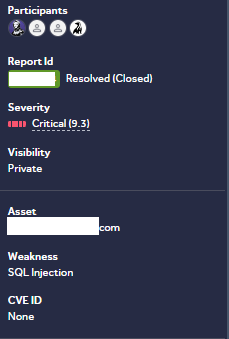
2. Deep Dive: Authenticated Time-Based SQL Injection
Once the KYC gate was bypassed, I analyzed the authenticated API traffic. An endpoint used for managing records caught my attention due to its parameter handling.
- Target Endpoint:
POSThttps://api.[REDACTED].com/api/case - Vulnerable Parameter: …Id
- Payload:
'XOR(if(now()=sysdate(),sleep(4),0))XOR'Z - Observation: The server responded with a consistent 4-second delay, confirming that the backend was executing the injected SQL command.

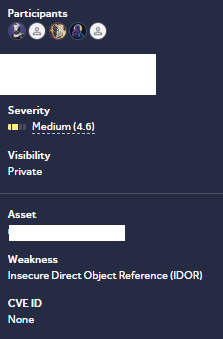
3. Expanding the Attack Surface: Double IDOR (Create & Delete)
The lack of proper authorization checks extended to object-level references, allowing for complete manipulation of other users' data.
A. Unauthorized Record Creation
- Vulnerability: IDOR in the owner identification parameter.
Exploit: By modifying the ....Id in the POST /api/case request (e.g., from my ID to a victim's ID), I could create or update records on behalf of any user.
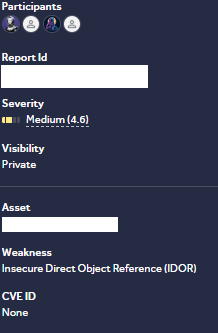
B. Unauthorized Record Deletion
- Vulnerability: IDOR in the delete endpoint.
Exploit:
- Intercept the delete request:
POST /api/case/[ID]/delete. - Change the object ID to a victim's ID.
- Result: The system deleted the victim's record without verifying if the authenticated user was the actual owner.
Stay Connected
- X (Twitter): @xelcezeri
- LinkedIn: Samet Yiğit

