Executive Summary
This report investigates a malicious executable masquerading as a PDF document (budget-report.pdf.exe). My analysis identifies the sample as a Trojan-type infostealer utilizing classic social engineering tactics (icon masking) combined with persistence mechanisms and encrypted C2 communication. The malware exhibits self-deletion capabilities and re-establishes itself under a disguised system service name to evade detection.

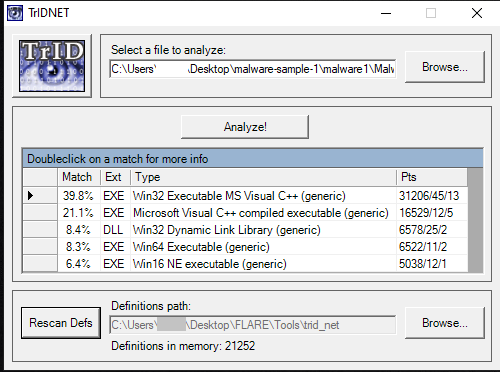
File Identification & Metadata
The sample leverages a double extension and a PDF icon to exploit default Windows settings that hide known file extensions.
- Filename:
budget-report.pdf.exe - MD5:
d7cc6c987c68a88defdab3a59070777e - SHA256:
15cc3cad7aec406a9ec93554c9eaf0bfbcc740bef9d52dbc32bf559e90f53fee - Type: Win32 Executable (PE32)
- Entropy/Signature: TridNET analysis confirms a ~60% match for a standard Windows Executable.
Static Analysis & Triage
Examination of the Portable Executable (PE) structure reveals several red flags in the Import Address Table (IAT) and string data.
Library & API Analysis
- Networking (
WININET.dll,WS32_32.dll): The inclusion of these libraries indicates the capability for low-level socket manipulation and high-level HTTP communication.

- Persistence (
RegSetValueExA): Direct evidence of the binary's intent to modify the Windows Registry for automated execution. - Execution (
ShellExecuteA): Provides the ability to spawn additional processes or execute shell commands. - Web Interaction (
InternetOpenA,InternetOpenUrlA, InternetReadFile): Confirms the binary is designed to reach out to external URLs, likely for stage-two payloads or C2 check-ins.

String Obfuscation
Despite the presence of legitimate strings, the extraction of networking-specific symbols such as socket, ioctlsocket, send, and recv aligns with the functionality found in the IAT, pointing toward data exfiltration capabilities.
Dynamic Analysis & Behavioral Patterns
The sample was detonated in an isolated environment with monitoring tools (Procmon, Regshot, FakeNet-NG) active to capture state changes.
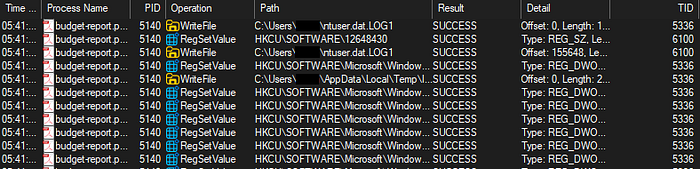
Persistence and Evasion
Upon execution, the malware initiates a self-protection and persistence routine:
- Registry Manipulation: A new key is generated at
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce\*12648430. This ensures the malware executes upon every user login.

2. Self-Deletion & Relocation: The original binary performs a self-deletion (melting) routine to remove the initial "entry" evidence. It then copies its logic to AppData\Roaming\12648430\ADService.exe.
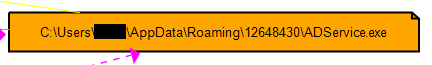
3. Masquerading: The relocated binary adopts the name "ADService" to blend in with legitimate Active Directory or administrative background tasks, while maintaining the fraudulent PDF icon.
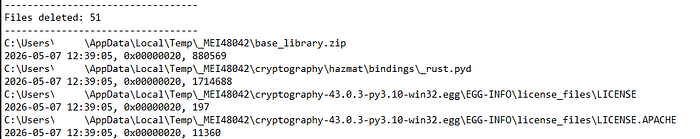
System Impact
Differential analysis via Regshot revealed a high volume of system noise, including over 20,000 registry key deletions and 51 file deletions, suggesting an aggressive cleanup or anti-forensics phase post-infection.

Network Forensics & Data Exfiltration
Traffic captured via FakeNet during the detonation phase confirms active communication with a malicious actor.
- C2 Domain:
mbaquyahcn.biz - Endpoint:
/uan9Bau3LJ9/ - Protocol: HTTP POST (Port 80)
- Exfiltration Profile: The malware sends consistent 938-byte packets at regular intervals. The payload is prefixed with
a=followed by a heavily encoded string.
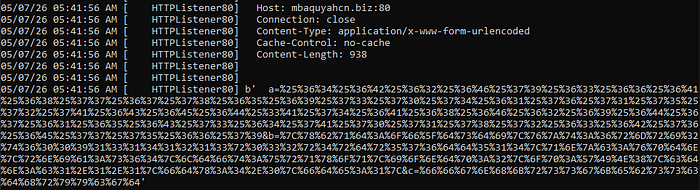
Payload Decoding
Preliminary decoding of the exfiltrated string reveals a structured data format containing system environment variables: dkboycfjhwgxeisptavqurzlnm:tjhobimgaelsdzpqxrckvnwufy&b=|xbqd:of_dsdi|vzt:6rmri2t600913141213r032r4rdr576dd514|qnzc:vpdn|rnia:s64|ldft:urqxoq|iondp:2|op:WIN8|cdn:c1.1.1|fdx:4.0|fde:1|&c=ffgnhkrssgkebsscdhryycgd
Key Extracted Data:
- OS Version: Windows 8 (
op:WIN8) - Architecture: x64 (
rnia:s64) - Framework: .NET 4.0 (
fdx:4.0) - Encoding: Multi-layered obfuscation, likely involving a custom substitution cipher or XOR before the final transmission.
Conclusion & Indicators of Compromise (IOCs)
This sample is a classic example of an infostealer utilizing basic but effective persistence and evasion techniques. The shift from a "budget report" to a background "ADService" demonstrates a clear intent to remain on the host for long-term data harvesting.
IOCs:
- MD5:
d7cc6c987c68a88defdab3a59070777e - C2 Domain:
mbaquyahcn.biz - File Paths:
%AppData%\Roaming\12648430\ADService.exe - Registry Keys:
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce\*12648430
