A Real-World Bug Chain Story
👋 Hey Hackers!
I'm MD Aariz Rahman (AKA 0x0meowsec) 👾
What started as a simple misconfiguration turned into a full vulnerability chain that could block users from accessing their accounts.
Let me walk you through it 👇
🧠 How It All Started
I was testing a target, just doing normal recon and exploring endpoints.
While browsing around, I came across an API path that looked like it might store user media.
https://api.example.com/media/profile_pictures/Out of curiosity, I opened it in my browser…
And yeah — that's where things got interesting 💀

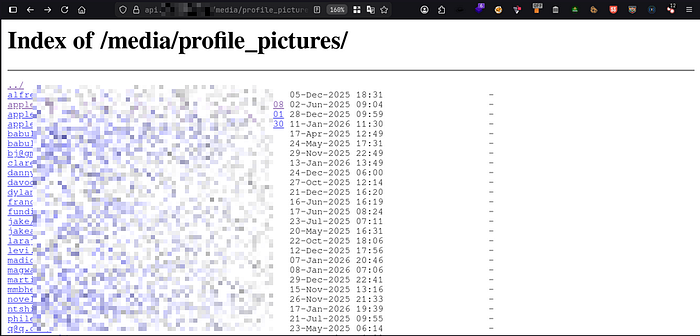
🔍 Step 1: Directory Listing Exposure
The endpoint returned a public directory listing.
No authentication. No restrictions. Just open.
But the real issue wasn't just the listing…
It was what was inside.
👀 What I Found
Instead of random file names or IDs, the folders were named like this:
user1@gmail.com/
john.doe@yahoo.com/
someone@company.com/Yep… real user email addresses exposed as directory names.
At this point, I could easily:
- Collect valid user emails
- Perform user enumeration
- Prepare targeted attacks
But I didn't stop there 😏

🔄 Step 2: Testing Email Change Functionality
Next, I moved to account settings to check how the email update feature works.
And this is where things got spicy 🔥
🧪 My Test Setup
I created two accounts:
- Account A →
victim@email.com - Account B →
attacker@email.com
Then I tried something simple…
👉 Changing Account B's email to the victim's email.
PUT /api/user/update-email
{
"email": "victim@email.com"
}And surprisingly…
✅ The request was accepted.
🚨 What Was Missing?
- No email uniqueness check
- No verification (OTP / confirmation link)
- No ownership validation
Basically… the system trusted me too much 💀
💥 The Breaking Point
Now both accounts had the same email.
So I logged out and tried logging back in using that email…
💀 HTTP 500 Internal Server Error
The authentication system completely broke.

🔗 Chaining the Bugs
Now comes the fun part — chaining both vulnerabilities.
Full Attack Flow:
- Extract emails from the directory listing
- Choose a target email
- Create a new attacker account
- Change attacker's email to the victim's email
- The system now has duplicate emails
- Authentication fails
Final Result
- The legitimate user can't log in
- The account becomes inaccessible
- This can be repeated for multiple users
🎯 Final Thoughts
This was a perfect example of why bug chaining matters.
Individually, these bugs were impactful… But together, they created a much bigger issue.
👉 From leaking emails 👉 To breaking authentication entirely
All from just a bit of curiosity and deeper testing.

🧑💻 That's It!
Keep hunting, keep learning… and always try to chain bugs for maximum impact 🚀
