You've decided you want to break into cybersecurity specifically the defensive side or what we usually call blue teaming, SOC analysis, incident response, you get the idea.
You've done your research, you know it's a growing field, and you're genuinely motivated. So you open up a browser tab, type "learn cybersecurity" into Google, and land on Udemy.
Two hundred and twenty-seven courses, in the security category alone.
You scroll, filter by rating, read descriptions that all sound equally important and equally urgent such as Ethical hacking, IT fundamentals. Terraform, Cloud security and somewhere in there, buried under the noise, is presumably the exact starting point you need except nothing is telling you which one it is or why.
This is the moment where most aspiring blue teamers don't quit because the material is too hard. They quit because they can't figure out what material to even start with. The chaos of the ecosystem defeats them before a single lesson has been watched.
So let me fix that for you. Here my structured roadmap I'd hand to anyone starting from zero in blue teaming in 2026 covering exactly what to study, in what order, and why each step earns its place in the sequence.
Build the Foundation Before You Touch a SIEM
The single most common mistake I see from people entering blue teaming is trying to skip the IT fundamentals layer because it feels unsexy.
They want to analyze malware and hunt threats, not study the OSI model. I understand the impulse. But skipping this layer is precisely why so many people hit a wall six months in and can't figure out why things aren't clicking.
Your first stop is the TryHackMe Pre-Security path. No prior IT background required , that's the entire point of it.
It walks you through offensive and defensive security basics, network fundamentals like the OSI model, packets and frames, DNS, HTTP all presented in an interactive, lab-driven format that doesn't drown you in abstract theory.
Then it moves into computer fundamentals: virtualization concepts, operating system basics, and introductory programming in Python and JavaScript.
This is the scaffolding everything else gets built on. Do not skip it.
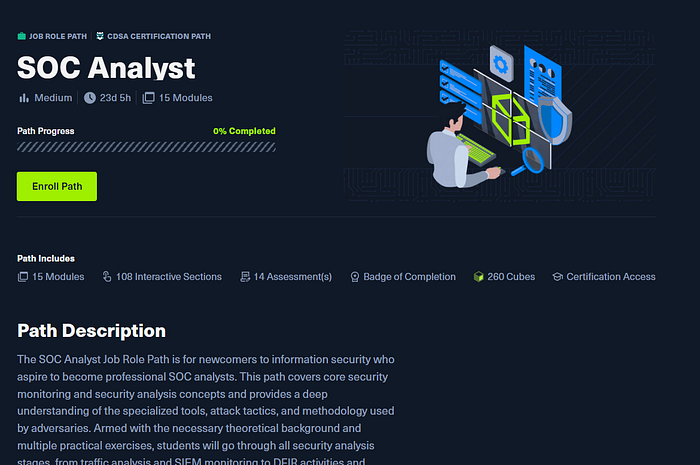
If TryHackMe isn't your preferred platform, the direct equivalent on HackTheBox is the SOC Analyst Prerequisites module.
The content covers similar ground such as Linux fundamentals, Windows fundamentals, networking, command line, web requests with some additions like Active Directory basics and the penetration testing process that reflect HTB's orientation toward the CDSA certification track.
The core rule here is simple: pick one or the other, not both. Pre-Security and SOC Analyst Prerequisites are parallel tracks covering the same conceptual territory. Choose your platform and commit.
Getting Hands-On with Defensive Concepts
Once the fundamentals are solid, the next stop is the TryHackMe Cyber Security 101 path. This is where you transition from passive knowledge to active skill-building, and it's where the actual blue team toolset starts appearing.
A few things in this path deserve particular attention.
Windows and Linux command line : I'll be blunt about this one. If you cannot navigate the command line in both operating systems with reasonable fluency, stop and address that before moving forward.
Not because someone told you to, but because virtually every investigative workflow in a SOC environment runs through the command line. Logs, process analysis, file inspection, network queries all of it. This is non-negotiable.
Wireshark and tcpdump : your network sensors are capturing packets continuously. When an incident occurs, you will have a PCAP file to analyze. These tools are how you read it. Learn the basic filters, understand packet operations, know what you're looking for. Wireshark in particular appears throughout every subsequent stage of your career.
SIEM fundamentals : the Cyber Security 101 path includes an introduction to SIEM concepts, and this matters because the SIEM is the technological heart of any SOC. Before you touch Splunk or Elastic, you need to understand how SIEMs work , log aggregation, correlation rules, alerting logic. The intro room builds that mental model before you're asked to operate the tools themselves.
There's also Metasploit coverage in this path. If you're aiming purely for blue teaming, Metasploit isn't immediately essential but I'd push back against ignoring it entirely.
Understanding the attack techniques and tooling that adversaries use gives you a meaningful advantage as a defender. Consider the offensive sections optional for now, but mark them for later. They become increasingly necessary as you progress.
The digital forensics section and the remnux rooms are genuinely valuable and often underestimated. Digital forensics isn't just for law enforcement , understanding how to handle evidence, read file metadata, and establish a chain of custody is relevant to real SOC work, particularly when incidents escalate to legal or compliance proceedings.
SOC Level One
With fundamentals and security basics under your belt, you're ready for the TryHackMe SOC Level One path, which received a significant update in 2026 with new content, new labs, and revised modules.
This path is designed to give you the knowledge required to operate as a junior SOC analyst , Tier One, the people who triage alerts, investigate initial indicators, and escalate what they can't resolve.
A few honest words about this role before diving in: AI is genuinely disrupting Tier One SOC work. Tools are automating alert triage at a pace that is compressing the demand for purely reactive, low-context analysis. I won't pretend otherwise.
That said, the knowledge in this path remains foundational not because the role is static, but because everything above Tier One is built on top of it. You cannot do Tier Two analysis without understanding what Tier One does. You cannot build detection rules without knowing what you're detecting. The path still matters. Just approach it as a foundation for growth rather than a destination.
What you actually learn here:
SOC processes and structure : the three pillars of any SOC are people, technology, and processes. Section two of this path walks through all three. This is institutional knowledge that most online courses skip in favor of tool demos, and it's the difference between someone who can use Splunk and someone who understands where Splunk fits inside an operational response workflow.
SIEM tools in practice : specifically Splunk and Elastic Stack. You don't need to master every SIEM platform in existence. Splunk and Elastic are the dominant tools in the market, and learning their query languages and alerting frameworks is a practical, high-value investment. QRadar and AlienVault exist and matter in specific environments, but start here.
The Cyber Kill Chain and MITRE ATT&CK : these two frameworks are the shared language of SOC environments. The Kill Chain gives you a model for understanding the stages an attacker moves through. MITRE ATT&CK gives you a granular taxonomy for classifying specific tactics and techniques. Together, they're how you build attacker profiles, structure investigations, and communicate findings to colleagues and leadership. Learn them properly.
Phishing analysis : I want to dwell on this one because it's underappreciated. Phishing is statistically the most common initial access vector in enterprise compromises. A disproportionate percentage of incidents you'll investigate in a real SOC trace back to a phishing email. Understanding how to analyze email headers, identify spoofing, decode obfuscated links, and recognize the infrastructure patterns attackers use isn't a beginner skill to rush past — it's a core analytical capability you'll use constantly.
Malware concepts :you will not be doing deep reverse engineering at Tier One. That work gets escalated to Tier Two and Three analysts who specialize in it. But you need to understand what malware is, how it behaves, what indicators it leaves behind, and how to handle a sample correctly when you acquire it from an endpoint. The malware section in SOC Level One gives you that conceptual foundation.
Again, if you prefer HackTheBox, the HTB SOC Analyst path covers equivalent ground , incident handling processes, security monitoring fundamentals, Windows and Linux logging, threat hunting with Elastic and Splunk, network traffic analysis. Same rule applies: pick one track and go deep rather than doing both.
Intermediate Work : SOC Level Two
TryHackMe SOC Level Two is where things get genuinely interesting, and where the work stops feeling like fundamentals review and starts feeling like real analytical capability.

A few highlights worth calling out specifically:
Advanced Splunk :this path goes deep on SPL (Splunk Processing Language), building queries from scratch, troubleshooting configurations, and fixing things that break in production.
There's a dedicated room literally called "fixit" that walks you through real Splunk errors. This is the kind of practical operational knowledge that doesn't appear in most courses but absolutely appears in real jobs.
Threat hunting and intelligence :this is probably the most significant capability jump between SOC Level One and Level Two.
Threat hunting means proactively searching your environment for indicators of compromise before an alert fires using intelligence about current adversary infrastructure, tactics, and techniques to look for things your rules haven't caught yet. This is where the work becomes analytical rather than reactive, and it's also where AI has the hardest time replacing human judgment. Good threat hunters are and will remain valuable.
Detection engineering : building the rules that generate the alerts Tier One analysts triage. Understanding how detection rules are constructed, what makes them effective, and what creates false positive noise is a Tier Two and above skill. If you're here, you're no longer junior.
Static and dynamic malware analysis : basic reverse engineering concepts appear at this level. Not expert-level binary analysis, but enough to understand what a sample is doing, how to run it safely, and what artifacts it produces. This is the gateway to deeper specialization if that direction interests you.
Practice Environments That Fill the Gaps
Once you've completed the path structure above, there are two categories of additional practice worth pursuing.
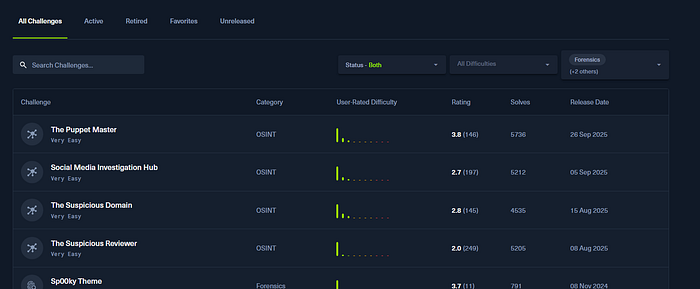
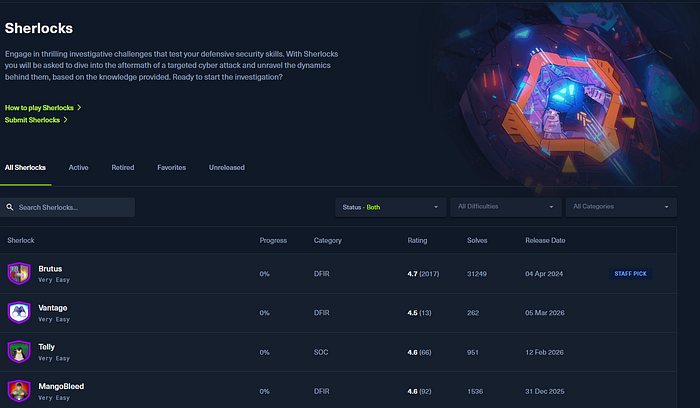
HackTheBox Challenges and Sherlocks: in the HTB challenges section, you can filter by category: forensics, OSINT, reversing, and cryptography are all directly relevant to SOC work. Sherlocks are purpose-built defensive labs organized around DFIR, cloud forensics, SOC scenarios, and threat intelligence cases. These are excellent for deepening specific skills outside the structured path format.
Cloud SOC : this is the gap most blue team curricula don't address adequately. Most learning resources focus on endpoint-centric SOC environments, but the reality of modern enterprise infrastructure is that significant workloads live in AWS, Azure, or Google Cloud.
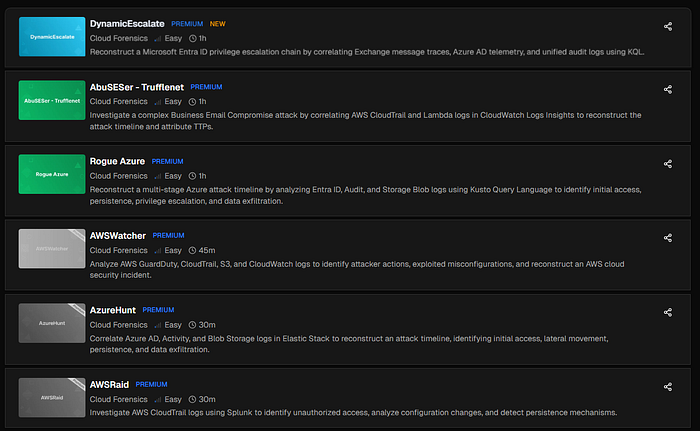
Investigating incidents in cloud environments requires different tooling, different log sources, and different investigative techniques than traditional endpoint SOC work. If your target employers operate cloud infrastructure and most do , adding cloud SOC capability is a genuine differentiator.
The CyberDefenders platform has a strong catalog of cloud forensics labs across all three major providers.
Lastly for Cloud SOC, you can check out my FREE courses below:
Certifications
Here's the practical certification alignment based on where you are in the path:
If you're working toward BTL1 (Blue Team Labs Level 1), your primary preparation should be SOC Level One on TryHackMe, supplemented by the Blue Team Labs official content (which you should prioritize over third-party material when preparing for a vendor-specific exam) and CyberDefenders' SOC v1 labs.
For CDSA (HackTheBox Certified Defensive Security Analyst), the preparation load is heavier , SOC Level One, SOC Level Two, and additional Splunk practice. CDSA is reportedly more demanding than BTL1, and the extra preparation reflects that density.
The broader principle is this: use whatever structured path you follow to build the skill set, then use the official certification preparation materials in the final stretch to align with the specific exam format and scope.
Your SOC Analyst Cheat Sheet
At the end, I've organized my pick of blue team certifications and mapped suitable online labs that you should practice while preparing in addition to most popular tools used by SOC analysts all in one interactive sheet that allows you also to track your progress:

Lastly
The blue team learning landscape isn't actually as complicated as it appears when you first encounter it.
The path is straightforward once you can see it clearly:
Pre-Security or SOC Analyst Prerequisites → Cyber Security 101 → SOC Level One or HTB SOC Analyst → SOC Level Two → Cloud SOC Labs → Certification preparation.
The map exists. Now you just have to walk it.

