In 1865, the British Parliament passed a law that has since become a symbol of technological fear. It mandated that a person carrying a red flag must walk ahead of every self-propelled carriage, warning pedestrians and horse-drawn traffic of the danger. Speed was limited to 2 miles per hour in populated areas and 4 miles per hour elsewhere. The law did not ban automobiles. It attempted to force a breakthrough technology into the logic of the past, where safety was ensured by visible control and physical predictability. We smile when reading about it today. But we are living at exactly the same breaking point: instead of steam carriages, we face generative artificial intelligence; instead of dirt roads, a global information network; and instead of wagons, traditional institutions of trust.
For a long time, the idea of a bodily digital identifier provoked instinctive rejection. The word "chip" carried associations with veterinary tracking, loss of autonomy, and total control. But logic, not emotion, must dictate the architecture of the future. When any text, voice, image, or expert opinion can be generated in seconds at zero marginal cost, anonymity ceases to be a shield. It becomes a vulnerability. In a world where everything can be forged, the only remaining value is the unforgeable origin of the signal.
This document does not advocate for surveillance or propose technologies that restrict freedom. It proposes a paradigm shift: from fragile trust in external devices that can be lost, broken, or deceived, to a cryptographic anchor inseparable from its biological carrier. We will trace a path from the diagnosis of the current trust crisis to an engineering solution that bypasses psychological resistance, leverages existing infrastructure, and restores to humans the right to be authentic in digital space. The time has come to lay down road markings. And we must begin not by trying to limit technology, but by returning accountability and verifiability to where they originate — to the human being.
PART I. DIAGNOSIS: THE TSUNAMI OF PLAUSIBILITY
The Death of Scarcity and the Birth of Synthetic Identities
For centuries, the dissemination of knowledge was governed by scarcity. Publishing an article, producing a film, or maintaining an expert column required time, resources, education, and reputation. These barriers were imperfect, but they served a critical function: they acted as a natural filter. Errors were expensive. Nonsense was weeded out by editorial boards, limited print runs, and the physical impossibility of mass-producing unverified material. Scarcity was protection.
Generative AI destroyed this law within a few years. The cost of creating text indistinguishable from the work of a graduate student, a financial analyst, or an investigative journalist approaches zero. The barrier to entry no longer exists. Anyone with access to a basic language model and minimal prompt-engineering skills can generate, in minutes, a "scientific paper" with proper structure, citations, formulas, and even simulated "research limitations." Superficially flawless. Substantively empty.
The scientific community and media industry have fallen into a trap they were unprepared for. Peer reviewers, who once evaluated dozens of manuscripts a year, now face hundreds of texts, each requiring verification not for plagiarism, but for factual validity, reproducibility, and originality. Journals are drowning. Editorial policies are tightening, but this only slows the flow without changing its nature. Students submit essays that only a narrow specialist deeply immersed in the field can distinguish from original work. Journalism loses its monopoly on fact: every news event is instantly surrounded by dozens of "analytical" pieces generated to fit a specific agenda or emotional trigger.
The tragedy is not that people think worse or that experts are lazy. The tragedy is that the filtering system, built on scarcity, is broken. Previously, generating plausible content required effort, and that effort served as a guarantee of at least minimal verification. Today, effort is decoupled from outcome. We are entering an era where the quantity of plausibility vastly exceeds the quantity of truth. In such an environment, survival belongs not to those closest to facts, but to those whose content is best optimized for attention algorithms and emotional response.
This is a fundamental shift in the ecology of knowledge. Information used to be the primary value. Now, the primary value is the origin of information. Until we have a cryptographically verifiable anchor linking a digital trace to a real subject, any text, image, or voice will default to being treated as potential synthetic noise. This is not paranoia. It is information hygiene for a society that has not yet realized it has transitioned from an era of rare messages to an era of infinite echo.
Content scarcity is dead. It has been replaced by trust scarcity. And until we close this gap, neither science, nor economy, nor public discourse can function as before. The next step is obvious: if content cannot be trusted, the source must be. But how do we ensure the source is a living person, not an algorithm simulating an identity? The answer to this question defines the architecture of the next decade.
Epistemological Collapse
If synthetic identities shatter trust in the source, their mass production leads to a systemic failure of the very mechanism of knowledge acquisition. We are entering an era where the problem is no longer that people spread lies. The problem is that the environment has become so saturated with plausible noise that distinguishing truth from imitation requires disproportionate investments of time, expertise, and computational resources. This is not merely an information crisis. It is an epistemological collapse: the disintegration of shared foundations upon which society agrees on what constitutes fact versus opinion.
When Noise Sounds More Convincing Than Truth
Human perception was never calibrated to filter machine-generated content. Our cognitive heuristics evolved in an environment where textual complexity correlated with authorial effort, where speaker confidence usually implied experience, and where argumentative consistency indicated thorough analysis. Artificial intelligence has hacked these heuristics. It generates structured, grammatically flawless, emotionally calibrated texts that activate the same neural trust patterns as works by real experts.
The paradox is that noise no longer merely drowns out the signal. It imitates it. Neural networks do not write nonsense. They write the "average" of the human knowledge corpus, stripped of risky hypotheses but saturated with markers of competence: citations, methodological caveats, correct terminology. To an unprepared reader — and often to a specialist forced to analyze hundreds of materials daily — this simulation appears more convincing than the cautious, nuanced voice of a real scientist. Truth becomes "boring" because it requires context. Noise becomes "bright" because it is optimized for attention.
Expertise erosion is accelerated by the fact that traditional knowledge institutions cannot adapt their reputation metrics quickly enough. Citations, h-indices, editorial recommendations — all can now be simulated or inflated by distributed networks of synthetic accounts. When reputation ceases to be a reliable proxy for quality, society loses its compass. A "leveling-down" effect emerges: when everything sounds professional, people stop orienting themselves by content and start relying on emotional resonance, mention frequency, or affiliation with familiar information bubbles.
Why Current Moderation Systems Are Doomed
The content verification infrastructure we use today was designed for a world where text production was the bottleneck. Moderators, fact-checkers, duplicate-search algorithms, anti-plagiarism systems — all operate in a "post-factum" paradigm. They react to already-published material, compare it with known samples, and look for overlaps or explicit violations. In the era of generative AI, this model loses meaning for three fundamental reasons.
First, cost asymmetry. Generating a thousand variations of an article takes AI seconds and fractions of a cent. Verifying one takes a human hours, an expert group days, and a distributed verification system weeks. The speed of synthetic content propagation outpaces the speed of its refutation by orders of magnitude. This is not a technical problem solvable by adding servers or training more moderators. It is a structural imbalance that makes any reactive system inherently lagging.
Second, evolution of detection evasion. Modern language models already vary syntax, imitate "human" errors, and avoid statistical patterns used by detection algorithms. Fighting AI-generated content becomes an arms race where defenders constantly update signature databases while attackers simply adjust the "temperature" of generation or add random noise. In such a game, the winner is not the most accurate detector, but the fastest generator.
Third, the cognitive limit of the user. Even if a platform labels material as "likely AI-generated," this does not guarantee correct perception. Studies show that content-origin warnings are often ignored if the message is emotionally charged or confirms existing beliefs. The filter works at the interface level, but not at the trust level. And trust is not a browser setting. It is a social contract that fractures under overload.
Devaluation of Trust as the Final Product of Overload
The most dangerous outcome of this process is not mass belief in a specific lie. It is mass belief that truth is fundamentally inaccessible. When any fact can be challenged by an "alternative source," when any video can be declared a deepfake, when any expertise can be replicated by an algorithm in five minutes, society shifts into defensive cynicism. People stop trusting not because they became less intelligent. They stop trusting because the cost of verification exceeds the subjective value of the result.
This cynicism does not liberate. It paralyzes. In a world where "everything could be fake," the need for proof, peer review, and dialogue based on shared facts disappears. Coordination mechanisms — from scientific collaborations to court proceedings, from stock markets to emergency services — begin to fail. Banks introduce multi-factor checks that users perceive as bureaucratic arbitrariness. Journalists publish materials with disclaimers that devalue the message itself. Scientists abandon open preprints, fearing their ideas will be appropriated or distorted by bot networks before peer-reviewed publication.
Trust, accumulated over centuries by institutions, is not destroyed maliciously, but entropically. Like metal fatigued by cyclic loads, it does not crack from a single blow, but from millions of micro-impacts. And when the crack reaches critical size, the system does not explode. It simply stops transferring the load. Information no longer leads to action. Statements no longer carry consequences. Opinions no longer shape agendas. They merely exist in parallel streams, neither intersecting nor challenging each other.
The Breaking Point
Epistemological collapse is not a verdict. It is a diagnosis pointing to the need for an architectural shift. As long as we try to filter content, we lose. As long as we try to teach people "media literacy," we delegate to individuals a task that exceeds the capacity of any education system by scale. The way out lies not in the plane of content, but in the plane of origin. Not "what was said," but "who said it and how can it be verified." Not "is the text true," but "is it anchored to an unforgeable source."
Without this shift, any attempt to restore order will resemble bailing out a sinking ship with a teaspoon. Noise will grow. Truth will demand ever more effort to defend. Trust will devalue to zero. But if we accept that in an era of infinite generation the only scarce resource becomes verifiable origin, we obtain the key to a new road marking. A marking that does not forbid speech, but demands accountability. A marking that does not destroy anonymity, but separates it from the right to influence. A marking that does not replace human judgment, but gives it a foothold in a world where simulation has become cheaper than the original.
The next step is to understand how to build this foothold so that it does not become a tool of control, but remains a tool of protection. And for that, we must first honestly acknowledge: the old trust contract, based on passwords, screen fingerprints, and faith in a "digital trail," no longer works. We need an anchor that cannot be lost, stolen, or forged. An anchor that is always with its owner. And this is where we transition from diagnosis to the architecture of the solution.
PART II. ANCHOR ARCHITECTURE: WHY THE BODY, WHY THE JAW
The Illusion of Invisibility and the Engineering Imperative
In the modern world, there is no such thing as an "invisible" person. The paradox is that we fear a hypothetical bodily marker, yet voluntarily carry a device that collects hundreds of times more data about us. The smartphone has long become the center of behavioral tracking, a payment terminal, and a digital passport. It continuously builds profiles, aggregates them, and sells them to brokers. Formally, we "agree" to privacy policies, but without accepting them, the device loses half its functionality. This is digital feudalism, where you rent convenience by paying with digital sovereignty.
Refusing a bodily marker does not make you free. It makes you dependent on a fragile, external, and alien infrastructure. Your account can be blocked, your phone stolen, your SIM cloned, your cloud biometrics leaked. A new generation of bodily identifiers changes this architecture. It returns the right to sign to where it originated — the physical carrier. This is not a rejection of privacy. It is a rejection of dependency. A shift from the "trust, but verify remotely" model to the "confirm locally, own cryptographically" model.
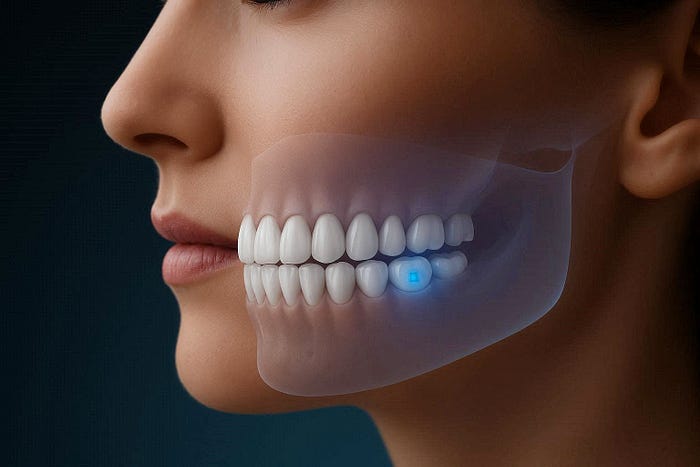
Convergence of Factors: The Jaw as the Optimal Node
When we conclude that digital sovereignty requires an anchor inseparable from a biological carrier, an engineering question arises: where to place the module? Anatomy, biomechanics, and the logic of mass deployment point to the jaw. This is not a compromise. It is the point of maximum convergence across four dimensions:
- Biomechanics and Osseointegration. The jawbone is living tissue capable of direct structural connection with titanium. Decades of dental practice have proven: the body does not reject the implant but integrates it into its own architecture. The bone provides rigid fixation, does not shift, protects the module from external impacts, and creates a natural "armored compartment."
- Energy Autonomy. Cyclic deformation during chewing and speech turns into a resource. Piezoelectric materials convert micro-vibrations into current. Additionally, inductive charging from the smartphone's NFC field during calls or payments is used. The module is not "always on." It is "always ready": it sleeps, wakes for milliseconds to sign, and returns to rest. This eliminates batteries, chemical degradation, and single points of failure.
- Bone as a Transmission Medium. Human bone is a natural waveguide. The ultrasonic range, inaudible and poorly penetrating through air, is ideal for secure transmission. The signal does not scatter into the ether or get intercepted remotely. The acoustic resonance of the jaw is unique: density, geometry, and trabecular microstructure create a biometric factor impossible to copy remotely. Bone conduction opens a direct audio channel to the ear, bypassing the external environment.
- Infrastructure and Psychology. There is no need to build new clinics. Dental implantation is a refined, globally scalable procedure with thousands of centers and protocols. Adding an optional "cryptographic module" to an existing implant specification is simpler than launching a new industry. Perception shifts: inserting titanium into the jaw is viewed not as an invasion, but as care, aesthetics, and restored quality of life. The cryptographic module becomes not a "tracking chip," but a premium function of a medical device.
PART III. CRYPTOGRAPHIC CORE: FROM FEAR TO MATHEMATICS
Four Fears and Engineering Reality
Instinctive rejection is a defensive reaction to uncertainty. But the threat has become invisible and algorithmic. To bridge the gap between emotion and engineering, we must match arguments with facts:
- "I will be tracked." The implant does not emit signals, knows no coordinates, transmits no telemetry. It is a "silent key." It sleeps until a trusted terminal sends a cryptographic request. Only then does it generate a one-time signature and return to sleep. The paradox: your smartphone is what continuously broadcasts your location. The bodily module replaces passive tracking with active, owner-controlled confirmation.
- "I will lose privacy." Privacy is often confused with anonymity. In the AI era, anonymity has become a vulnerability. Real privacy is control over data disclosure. Here, Zero-Knowledge Proof (ZKP) cryptography comes into play. The terminal asks: "Is the owner over 18?" The module computes the answer and returns only the mathematical proof "Yes." No name, no date, no geolocation leaves the body. You do not become transparent. You become verified, but closed.
- "I will be hacked or copied." Traditional keys are stored as static bits: extractable, copyable, transferable. The implant uses a Physically Unclonable Function (PUF). The key is not written. It is born from microscopic, random defects in the crystal lattice and its boundary with tissue. The module sends an acoustic CHIRP; reflection from the bone's trabecular lattice forms a unique interference pattern — this is the key. Upon attempted extraction, temperature change, or impedance shift, the structure is disrupted, and a hardware trigger physically destroys the PUF-reading circuit, rendering the key permanently uncomputable (
zeroization). It cannot be copied remotely—it does not exist as a file. Forging it is physically meaningless. - "This is a veterinary approach." A veterinary chip is a passive, non-cryptographic marker for external accounting. A digital anchor is a sovereignty tool, activated only by the owner's will. The difference lies in the narrative. Implanting titanium into the jaw is a medical act of care, not an administrative act of registration. Shifting the focus from control to autonomy neutralizes resistance at the perception level.
An Architecture You Can Trust
The combination of PUF, ZKP, and hardware zeroization creates a system that requires no blind faith in the manufacturer or regulator. Trust is built into physics. The key is not stored; it is computed. Privacy is not promised; it is mathematically guaranteed. Protection is not software-based; it is biophysical. This is a personal cryptographic vault that works only in symbiosis with the body and remains silent in any other situation.
The Duress Protocol: Graded Response to Physical Coercion
Any system claiming digital sovereignty must account for the scenario where sovereignty is attempted to be taken by force. Physical coercion is a known attack vector. The implant's architecture does not ignore this risk. It establishes a hidden signal mechanism, activatable without the aggressor's knowledge, leveraging the anatomical privacy of the oral cavity.
The jaw is the only zone where a person can perform precise, rhythmically organized movements invisible to an external observer. The module's piezoelectric matrix, already used for energy harvesting and acoustic communication, can distinguish not just mechanical contact, but its temporal pattern. Three sequential touches by the tongue, performed in a specified rhythm, create a vibrational signature that the local DSP reliably distinguishes from background activity like chewing, swallowing, or articulation. The signal is processed within a secure element, never leaving the body, and interpreted as a duress command.
The protocol is not binary. The architecture offers a graded response, configurable by the user during initialization:
- Covert Verification with Post-Trigger. The module generates a cryptographically valid signature that passes all technical checks. However, a duress flag is steganographically embedded in the transaction metadata. When the operation hits protected infrastructure (bank, registry, court system), the flag automatically triggers a freeze protocol: assets are locked, the transaction is paused, trusted contacts are notified. To the aggressor, the operation is complete. To the system, a countdown has begun.
- Temporary Isolation. The module simulates a hardware failure, ceasing to respond to requests. All cryptographic operations are blocked for a set interval (e.g., 30 minutes). The aggressor loses the coercion window. After the timer expires, functionality restores autonomously. Effective in scenarios where the attacker seeks a quick transaction, not prolonged detention.
- Hardware Zeroization. Irreversible physical destruction of the PUF-reading circuit. The key becomes uncomputable forever. The user activates this mode consciously in a direct threat situation, where preserving the digital identity poses a greater risk than destroying it. This is the ultimate act of sovereignty: the right to say "no" even when all other control channels are severed.
Why this is necessary and what it does not guarantee: The duress protocol does not offer 100% protection against a prepared opponent controlling every movement. But absolute protection is not the goal of engineering. The goal is to change the aggressor's calculus. Most coercion acts occur under time constraints and incomplete information. In these scenarios, the hidden signal triggers with high probability, and consequences unfold post-factum. The mere existence of an indisputable, documented mechanism turns every coercion attempt into a roulette. Furthermore, the protocol is not a backdoor. It is an owner's conscious configuration, set like emergency contacts. The module ceases to be a mindless executor. It becomes an ally capable of distinguishing consent from coercion via a signal known only to the owner. The throat may be choked. Hands tied. But as long as the anatomical channel remains free, the person retains their last word. And the architecture guarantees it will be heard.
PART IV. TRUST SYSTEM: GRADED IDENTITY AND NEW "TRAFFIC RULES"
Context-Dependent Trust Level
Digital life is not monolithic. Reading news, transferring funds, signing a contract, publishing a paper — all require different levels of confidence in the subject. Graded identity offers a third path between full anonymity and total disclosure: trust, scalable to context.
The system requests only the confirmation level adequate to the risk. Basic level — pseudonymous activity: confirming a unique living person without revealing a name. Sufficient for forums, bot protection. Medium level — contextual verification: proving age, residency, license via ZKP without transmitting raw data. High level — full cryptographic binding with non-repudiation for finance, courts, e-government, science. The action is signed by a key existing only in symbiosis with the body and tied to a timestamp. Forging or denying it is impossible without extracting the module, which triggers key destruction.
The user is not forced to reveal themselves everywhere or nowhere. They determine which trust level to present. Identity transforms from a static label into a dynamic risk-management tool. This defuses tension around "total surveillance." When infrastructure requests only the minimum necessary for context, the main argument of opponents disappears.
Separation of Persona and Avatar, AI Delegation
The fundamental shift is the decoupling of legal identity and digital avatar. The root key is born from the implant's PUF, never leaves the body, and only signs requests. Based on it, the user generates dozens of avatars with their own DIDs, reputations, and permissions. If an avatar is compromised, it is instantly revoked without affecting others. The system no longer depends on a "single account."
For AI agents, a scoped key delegation mechanism is introduced. You do not hand over the root key. You generate a temporary sub-key with strict metadata: validity period, operation limits, allowed platforms. Every agent action is signed with it and leaves a trace in the audit ledger. If the agent exceeds bounds — the transaction is rejected by the protocol. If it acts within bounds — legal responsibility falls on the root key owner. AI ceases to be a "black box." It becomes a tool with a clear mandate.
Sandbox for Dissent
The architecture provides an isolated layer with reduced trust for unverified sources. Here, one can publish alternative models, manifestos, experiments. Content is not deleted, but automatically marked at the transport level: the server, seeing no anchor signature, applies a "Unverified Source" header without analyzing content. It is not indexed in main databases, nor allowed in financial or scientific operations. This preserves space for marginal hypotheses but protects critical infrastructure from synthetic contamination. If an idea contains a grain of truth, it finds an endorser, passes verification, and moves to the main layer. Filtering stops being a wall. It becomes a ladder.
New "Traffic Rules" for the Digital Age
The red flag era ended not because cars became safer, but because society developed rules allowing technology to serve people. License plates, driver's licenses, road markings, insurance appeared. Not to kill freedom, but to make it predictable.
The digital world faces the same choice. "Traffic rules" for the information age will look like a trust infrastructure:
- Origin Marking. Every signal carries a cryptographic metadata tag about its initiator. Like a license plate: it doesn't reveal identity to everyone, but allows source identification upon violation.
- Access Stratification. The network splits into "highways" for verified participants (minimal latency, maximum trust) and "backroads" (anonymity preserved, but content marked as unverified).
- Digital Reputation and Accountability. The right to influence is tied to verified identity. Every bot or account is signed by a real subject bearing responsibility. The network transforms from a space of unpunished noise into an environment where trust becomes currency.
PART V. INFRASTRUCTURE AND ADOPTION: FROM TECHNOLOGY TO NORM
Don't Build — Certify
We do not need to erect a new industry from scratch. The global dental infrastructure already exists: ISO, FDA, and CE standards; millions of trained surgeons; refined supply chains. It is sufficient to add an optional cryptographic module to the specification of an approved implant. This is an engineering iteration, not a revolution. The regulatory pathway is predictable: the module is classified as a component of a medical device, eligible for accelerated approval by analogy. The adoption curve compresses to 5–7 years.
The key question is binding the key to the carrier. The answer: a network of authorized clinics as trust nodes. They do not store keys or see transactions. Their function is strictly limited: secure initialization, cryptographic binding to the owner's biometric profile, integrity verification during check-ups, and secure key migration upon replacement. The clinic is not an arbiter — it is a notary of physical presence. Initialization follows a multi-stakeholder protocol: the patient confirms identity via national eID, the clinic certifies the fact of implantation, and the module signs the activation act — no single party controls the process unilaterally. A decentralized but auditable network prevents monopolization and stimulates competition for quality.
The Sociology of Adoption: Desire, Not Dictate
Technologies do not scale through prohibitions. They scale through desire. Wireless charging, fingerprint scanners, noise cancellation — all began as premium options for enthusiasts. They became standards not by mandate, but through convenience and status. The cryptographic implant follows the same trajectory.
At launch, it is positioned not as a mass-identification tool, but as a premium function of digital sovereignty. "Your implant doesn't just hold a crown. It guarantees that only you can authorize a payment, confirm a document, or access a protected resource. No passwords. No phone. No risk of theft." Early adopters — IT professionals, financiers, lawyers — perceive it as an advantage. A new norm emerges: "true sovereignty begins where the key is inseparable from the body." Over time, the technology descends the price ladder, becoming a routine option in prosthetic dentistry.
Psychological judo does not manipulate. It aligns. Fear is a healthy reaction to uncertainty. Instead of pressure through arguments, an alternative optics is offered: voluntariness, medical legitimacy, personal benefit, and status appeal. Conspiracy theories lose fuel because the image of an "invisible hand" implanting trackers disappears. What remains is the dentist's office, a service catalog, and the patient's free choice. Free choice is the most powerful antivirus against fear.
Economic Gravity
The winner of the next decade will earn not from selling gadgets, but from architecting the trust layer. Not from monetizing attention, but from taxing certainty — confidence in the origin of an action. Licensing the protocol, verifying nodes, auditing key migration, supporting interoperability standards with IoT, banks, and e-government — this is a utility layer, like DNS or TCP/IP, but with built-in accountability. Whoever becomes the standard will operate atop all platforms and receive a microscopic but inevitable percentage from every act of trust in the digital economy. Eight billion people and tens of billions of devices requiring confirmed presence transform the consumer electronics market into a market for digital infrastructure. Value shifts from "hardware" to "network effects of trust."
PART VI. ANTICIPATING CRITICISM: SEVEN WALLS TO PASS THROUGH
Any technology claiming to reshape the infrastructure of trust must first pass through the fire of objections. Not because criticism is hostility. But because it is precisely in friction with strong counterarguments that engineering maturity is forged. Below are not excuses, but a continuation of the architecture. Seven walls that an honest project must acknowledge before inviting a person to step across the threshold.
1. "This will lead to forced implantation"
This is the most legitimate and most dangerous concern. History knows enough examples where a benevolent invention became an instrument of coercion. Therefore, the architecture must embed immunity at the protocol level — not at the level of promises.
The answer consists of three layers.
First, technological. The implant is not the only possible anchor. The protocol is open: PUF-based verification can be implemented in an exoskeletal module, a subcutaneous bio-glass, or a certified token with multi-factor binding. The jaw is the optimum, but not a monopoly. If society rejects the intra-bodily solution, the infrastructure of ZKP and graded identity remains functional on alternative carriers. The module in bone is the peak point of convenience, not the point of uniqueness.
Second, regulatory. The protocol is designed as an optional service embedded in a medical device that the patient chooses voluntarily anyway. Legislative fixation: "an implant with a cryptographic module is available only upon explicit informed consent and does not constitute grounds for granting or restricting civil rights." This is not a declaration, but a technical requirement: without user activation, the module remains an empty crystal. It does not sign, does not identify, does not turn on. A state may require a passport — it cannot require a specific physiological implementation of a key.
Third, social. Obligation arises only where the alternative is unbearable. If verified identity becomes so convenient that refusing it is economically irrational, pressure will emerge not from decree but from gravity. There is only one antidote to this: preserving a functional anonymous environment. The "backroads" must remain passable. Forums without verification, cash transactions, anonymous publications — these are not "enemies of the system," but its counterweight. Where there is a free exit, there is no prison.
2. "The body is a temple. Any intervention is desecration"
This objection cannot be defeated by logic, because it belongs to the plane of faith. But it can be respected and integrated. For religious and ethical groups, the protocol provides for an exocorporeal anchor — a device possessing the same cryptographic properties (PUF, ZKP, zeroization) but not penetrating beneath the skin. It requires more frequent maintenance, is vulnerable to theft and loss, but preserves the mathematical integrity of the system.
More importantly: the implant itself carries no "mark," transmits no number, is not a passive beacon. In religious symbolism, the "mark of the beast" is a sign of submission to external will, visible and mandatory. The cryptographic module is an invisible vault, activated exclusively by the carrier's will. It does not announce to the world, "here is my number." It remains silent until you choose to sign. From a theological perspective, this is closer to a seal that the owner applies with their own hand than to a brand applied to them.
3. "What if a new standard emerges tomorrow? You can't update hardware in bone over the air"
This is an honest engineering question. The honest answer: the implant is not a five-year smartphone. It is infrastructure for decades. Therefore, two principles are embedded in the specification.
First, minimalism. The module does not perform complex computations. It does not run neural networks, store databases, or process protocols. Its task is one: to generate a signature based on a physically unclonable function. PUF does not depend on algorithmic standards. No matter how many times hash functions and elliptic curves change, the physical imprint of the crystal remains. What is updated is not the hardware, but the signature policy, which is set by the external terminal. The module merely confirms: "yes, this key belongs to this body."
Second, modularity. The cryptographic node is designed as a replaceable cartridge inside a standard titanium abutment. Replacement is a procedure identical to changing a crown or micro-prosthesis: 20 minutes in the dentist's chair, local anesthesia, a refined protocol. This is not open-body surgery, but scheduled maintenance. The module's service life is 10–15 years, which aligns with the lifecycle of a dental implant. By that time, the medical component also requires inspection. Updating the standard becomes part of routine care, not an emergency intervention.
4. "This will create an elitist system: the rich inside, the poor outside"
Digital stratification already exists. Those who have the latest smartphone, digital banking, and biometric passports are inside. Those who do not are already cut off from finance, public services, and even public transport. The implant does not create this inequality. It offers a chance to neutralize it.
How? By lowering the cost of trust. Today, banks and platforms spend billions on anti-fraud and verification, embedding these costs in commissions paid by everyone. When identity confirmation becomes mathematically cheap and physically unforgeable, the cost of trust collapses. This lowers the entry barrier for basic financial and social services. The poorest segments of society suffer not from implants, but from the inability to prove their reliability. Verifiable identity is, ultimately, a credit of trust that no longer requires reputational capital accumulated over years.
Technology descends the price ladder. First — a premium option. Then — a standard in dental protocols. In a 10–15 year horizon, the module may become cheaper than a modern smartphone, because it is simpler: no screen, no battery, no camera, no operating system. It is a crystal in a titanium setting. Its cost is determined not by electronics, but by certification. And certification, unlike semiconductors, scales.
5. "Clinics or manufacturers will become new intermediaries — worse than the state"
Centralization is dangerous regardless of who sits at the center. Therefore, the architecture is built on distributed trust nodes. The clinic does not store keys. It does not see your transactions, does not know your avatars, cannot sign on your behalf. Its function is strictly limited: module initialization in the presence of a live patient, cryptographic binding of PUF to the owner's biometric profile, integrity verification.
This is the role of a notary of physical presence, not a keeper of secrets.
The key is not created at the factory. It is born at the moment of activation from chaotic micro-defects in the crystal and its boundary with bone tissue. The manufacturer cannot know the key in advance, because it does not exist until contact with the body. This is not a marketing trick. This is physics. PUF means that even with full compromise of the supply chain, an attacker obtains only a faceless crystal, which becomes unique only in the jaw of a specific person.
If a clinic or manufacturer attempts to embed a backdoor, the protocol will detect this during audit. Open specifications, third-party auditors, competition among nodes — none of this guarantees absolute honesty, but all of it guarantees absolute transparency. Trust is not required here. It is verified mathematically.
6. "Anonymity will disappear. Only total transparency will remain"
On the contrary. Today, anonymity is dead for those without specialized skills: your smartphone, bank, provider, and social networks all know more about you than you tell about yourself. True anonymity has become a privilege of narrow specialists. For the masses, it has turned into an illusion.
The implant returns privacy by separating uniqueness from disclosure. The basic level of graded identity proves only one thing: "a living person, not a bot farm, stands behind this action." Name, age, geography, biography — remain outside. ZKP allows answering questions without transmitting data. "Are you over 18?" — "Yes, and here is the mathematical proof." No date of birth, no passport, no tax ID. Only a bit of certainty.
Full anonymity is preserved in the "sandbox for dissent." There, neither implant nor verification is required. But there is also no access to critical infrastructure. This is not a ban. It is a separation of flows: a highway for verified actions and a backroad for free speech. Everyone chooses where to be.
7. "AI will still find a workaround. An army of bots will adapt"
This is not criticism of the implant. This is criticism of any protection. And it is only partially fair. Yes, AI will evolve. But the implant changes the game itself. Today, a bot bypasses CAPTCHA, imitates behavior, generates text. Tomorrow it will generate text even better. But it cannot generate the physical presence of a PUF in the jaw of a specific person. This is not a machine learning task. This is a task of physical intrusion.
The architecture is not built on stopping AI progress. It is built on shifting the line of defense from the plane of "content vs. content detector" to the plane of "presence vs. absence." While bots compete with moderation algorithms, it is an arms race that bots win due to cost asymmetry. But when it comes to a cryptographic signature tied to a biological anchor, a bot cannot participate in this race. It has no body. This is not an evolution of bypass. This is an a priori absence of the right to start.
Conclusion of the Section
Each of these objections is not an enemy, but an architect. They force the project to remain voluntary, decentralized, medically safe, and socially inclusive. A technology that does not withstand honest criticism deserves a red flag. But a technology that passes through it and emerges more precise deserves road markings. We offer not faith in a miracle. We offer engineering that acknowledges its boundaries and works flawlessly within them.
INTERLUDE: THE WORLDCOIN LESSON, OR WHY BORDER CONTROL WON'T REPLACE A KEY
The moment we assert the necessity of a cryptographic anchor inseparable from the body, an inevitable question arises: how does this architecture differ from the most prominent project in the digital ID niche — Worldcoin? The question is fair. And the answer simultaneously constitutes the strongest argument in favor of "The Wisdom Tooth Solution."
Both projects start from the same diagnosis: generative AI has destroyed the scarcity of plausibility, and without proof of personhood, digital civilization loses its ability to distinguish will from noise. But their architectural responses differ radically.
Worldcoin builds a trust system from the outside. Its logic: if every living person has a unique iris, it suffices to create a global registry of these irises to prevent identity duplication. The Orb scans the eye, converts the image into a code, and issues a binary flag: human or not. This is elegant for mass filtering, but it creates an architectural ceiling. The Orb verifies humanity, but does not verify the origin of an action. It says: "This account belongs to a living person." But it does not say: "This specific document was signed by this specific body at this specific moment." The iris is a passive biometric template that can be photographed, reproduced, or transmitted as data. Moreover, dependence on a centralized scanning operator makes the system a target for regulators: from Kenya to the EU, the idea of a global biometric registry provokes justified fear.
Our architecture operates on inverse logic. We do not ask the world: "Is this person unique?" We give the person the ability to tell the world: "I am here, and here is the mathematical proof of my presence." The implant is not scanned by an external camera and does not enter a global database. The PUF key is born at the moment of contact between the crystal and living bone, from microscopic, non-reproducible defects. It cannot be recorded at the factory, copied remotely, or extracted without destruction (zeroization). This is not passport control. This is a notarial seal embedded in biology.
The difference changes everything. The Orb solves the task of mass filtering — it is good as a digital gatekeeper at the entrance. But a gatekeeper does not sign checks, notarize contracts, or bear legal responsibility. For high-stakes scenarios, a binary "human/not human" flag is insufficient; what is needed is graded identity and non-repudiation. Worldcoin offers a next-generation CAPTCHA. We offer an infrastructure for digital rights.
Adoption infrastructure and economics confirm the difference in scale. World must build its network from scratch: manufacturing devices, deploying scanning points, fighting regulatory bans. Implementation is tied to tokenomics (WLD for scanning), which breeds suspicions of exploitation and inflationary pressure. Our model requires no new industry. It leverages the refined dental infrastructure, protocols of informed consent, and the logic of technological diffusion: from premium option to routine standard. We do not monetize attention or buy trust with tokens. We create a utility layer, like DNS, that taxes certainty — confidence in the origin of an action.
The future will not choose between these approaches. It will combine them. Worldcoin will remain at the entry level: filtering synthetic noise in social networks and basic services. The cryptographic anchor in the jaw will become the standard where an error costs money, freedom, or reputation: in finance, courts, science, e-government. The Orb will say: "Yes, he is alive." The implant will say: "Yes, he signed, and behind this signature lies unforgeable origin."
We embed this lesson into the foundation of our model. Not as a replacement for external scanners, but as the next evolutionary step: moving trust to where it is physically invulnerable. Not accounting, but sovereignty. Not proof of humanity, but the right to sign.
CONCLUSION: THE MATURATION OF DIGITAL CIVILIZATION
True technological shifts are an evolution of acceptance. Seat belts provoked protests. Smartphones seemed like accessories. Vaccination was perceived as an invasion. Each time, society resisted not the technology itself, but the fear of the unknown. The dental cryptographic implant passes through the same filter. Today — instinctive rejection. Tomorrow — an option for connoisseurs of digital autonomy. The day after — a routine element of medical protocols. In a generation — an invisible background of civilization. This is not imposition. This is maturation.
What do we gain?
First — the end of the era of AI fraud. When a bank, court, or government service requires the physical presence of a cryptographic anchor, fake calls, forged video authorizations, and simulated panic on exchanges become technically impossible. No body — no transaction. No signature — no access. An algorithm can imitate a voice, but it cannot bear responsibility.
Second — the return of trust. Science, media, markets can once again rely on the source, rather than drowning in noise. When every opinion is tied to a verified subject, the need for manual moderation and endless fact-checking disappears. Trust becomes an architectural property of the network.
Third — freedom from gadgets. We will cease to be hostages to battery life, cracked screens, vulnerable clouds. The key is always with you. Access — instant. Responsibility — clear. You do not carry your digital identity in your pocket. You are it.
Overcoming the "red flag syndrome" requires a change in optics. In an environment where everything can be forged, analog invisibility becomes a blind spot. The 1865 law stifled progress by trying to force new speed into old frames of fear. Today we face the same choice: continue to display "red flags" in the form of prohibitions and censorship, or finally lay down road markings. Markings that do not restrict movement, but make it predictable. That do not take away freedom, but return the right to be authentic.
In an era where the cost of generating plausibility is zero, unsigned information defaults to zero. Text without an anchor, video without verified origin, a transaction without confirmed presence — all are automatically classified as potential synthetic noise. This is not censorship. This is information hygiene. Not the end of privacy, but its mathematical guarantee. Not the loss of humanity, but its last refuge in a world where machines have learned to imitate will, but cannot bear responsibility for it.
The future does not belong to those who try to slow AI down to the speed of human verification. It belongs to those who will build a system where technology serves humans. Where the key is inseparable from the body. Where trust is not given on credit, but verified mathematically. Where everyone can remain invisible, but no one can remain unaccountable. Digital civilization is maturing. And its first true step into adulthood is not a prohibition. It is a signature.

TECHNICAL APPENDIX
To the document "THE WISDOM TOOTH SOLUTION"
A. Biometric PUF Based on Bone Acoustics
The cryptographic anchor uses a Physically Unclonable Function (PUF), whose entropy source is the microarchitecture of the carrier's jawbone — a unique combination of density, geometry, and trabecular orientation.
Reading principle:
- Upon receiving a signature request, the module generates a short ultrasonic pulse — an acoustic CHIRP (Compressed High-Intensity Radiated Pulse) in a range that does not cause cavitation and is safe for bone tissue.
- The CHIRP propagates through the bone as a waveguide; the reflected signal, modulated by interference on the trabecular lattice and tissue boundaries, is registered by the module's piezoelectric receiver.
- The interference pattern is digitized, processed through a stable-feature extraction algorithm, and converted into a bit string serving as input for the cryptographic module.
- Inter-session variability is compensated by applying a fuzzy extractor (key extraction with error correction), enabling identical key generation despite natural bone state fluctuations while preventing collisions between different carriers.
PUF properties:
- Not stored as static bits; the key is recomputed on each request.
- Cannot be extracted non-invasively: remote reading lacks sufficient resolution; the acoustic channel is protected by attenuation in soft tissues and the requirement for direct contact.
- Cannot be cloned: duplicating would require reproducing the 3D microstructure of a specific person's bone with ultrasonic-wavelength precision, which is technically infeasible in the foreseeable future.
B. Hardware Zeroization
Protection against physical attacks is implemented at the hardware level and does not depend on firmware or external power:
- The module housing contains a network of conductive traces and sensors continuously monitoring integrity, temperature, surrounding tissue impedance, and unauthorized access attempts.
- Upon detecting an anomaly (tampering, supra-normal temperature change, loss of acoustic bone contact), a trigger irreversibly destroys the analog PUF-reading circuit (microsecond melting of key interconnects).
- As a result, the very possibility of restoring the unique response is physically eliminated — the key becomes permanently uncomputable.
- The zeroization state is verifiable upon subsequent external inspection: absence of the expected PUF response serves as proof of module compromise.
C. Initialization Protocol
To prevent man-in-the-middle attacks during anchor-to-legal-identity binding, a multi-stakeholder protocol with three-way control separation is applied:
- Patient presents a national electronic ID card (eID) with built-in electronic signature capability.
- Authorized clinic (implantology center) instrumentally confirms successful osseointegration and correct module operation, signing the corresponding act with its corporate key.
- Module, at initialization, generates its own PUF key, computes the corresponding public key, and signs a registration request for the trust registry, including a timestamp, module identifier, and hashes of patient and clinic attestations.
Only upon simultaneous presentation of all three signatures (patient, clinic, module) does the trust registry accept the entry. No single party can unilaterally initialize, substitute, or revoke the binding. The clinic does not gain access to the private key and does not participate in subsequent transactions.
D. Automatic Marking of Unconfirmed Content
In the trust infrastructure described, all content is divided into streams:
- Mainstream stream: messages and transactions signed by a key derived from the anchor.
- Peripheral ("sandbox") stream: messages lacking such a signature.
Marking is performed exclusively at the transport level, without semantic analysis:
- Upon receiving a message, the server checks for a valid signature certified in the trust registry.
- If the signature is absent or fails validation, the server automatically assigns the meta-header "Unconfirmed Source" and places the message in the corresponding index.
- No AI algorithm analyzes content; the decision is based solely on the absence of cryptographic anchor binding.

SOURCES AND STANDARDS
Historical Context & Sociology of Adoption
[1] UK Parliament. Locomotive Acts (Red Flag Act 1865). 1865. [Legislative Act] https://en.wikipedia.org/wiki/Locomotive_Acts Introduction, Part I, Part VI, Conclusion. Historical basis for the "red flag" metaphor: illustration of regulatory fear and attempts to fit breakthrough technology into past logic.
[2] Rogers, E. M. Diffusion of Innovations. 5th ed. Free Press, 2003. [Scholarly Monograph] ISBN 978–0743222099 Part V, Part VI. Adoption Curve theory confirming the deployment trajectory: from premium option to mass standard through desire and convenience, not administrative dictate.
[3] Linux Foundation & W3C. Decentralized Identity Economic Models. 2023. [Industry Report] https://identity.foundation/ Part V. Analysis of micro-tariffs for acts of trust, compatible with the "taxation of certainty" model and the shift of value from consumer hardware to the infrastructural trust layer.
Scientific-Engineering Base (Biomechanics, Energy, Acoustics)
[4] Delnavaz, A., Voix, J. Flexible piezoelectric energy harvesting from jaw movements. Smart Materials and Structures, 2014, 23(10). [Peer-reviewed Research] DOI: 10.1088/0964–1726/23/10/105020 Part II. Direct experimental confirmation of energy harvesting from jaw movements for autonomous powering of implantable devices.
[5] Fan, X. et al. Piezoelectric energy harvester utilizing mandibular deformation. Journal of Mechanical Science and Technology, 2019, 33. [Peer-reviewed Research] DOI: 10.1007/s12206–019–0749–4 Part II. Feasibility study of piezo-harvesting specifically from mandibular deformation, substantiating the "always ready" concept without chemical batteries.
[6] Cochlear Ltd. Bone Conduction Implants: Clinical Overview. [Medical Review] https://www.cochlear.com/us/en/home/diagnosis-and-treatment/how-cochlear-solutions-work/bone-conduction-solutions/bone-conduction-implants Part II. Confirms clinical maturity of transcutaneous bone conduction and long-term osseointegration of titanium in the jawbone.
[7] Dutta, K. et al. Risks and complications associated with dental implant failure. Clinical Implant Dentistry and Related Research, 2020. [Peer-reviewed Research] DOI: 10.1111/cid.12948 / PMC7518499 Part II, Part VI. Honest review of risks (peri-implantitis, osseointegration failure), necessary for balanced discussion of medical safety and replacement protocols.
Cryptography, Hardware Security & Protocols
[8] NIST. IR 8406: Physical Unclonable Functions (PUF). 2022. [Standard/Technical Review] https://csrc.nist.gov/publications/detail/ir/8406/final Part III, Appendix A. Official status of PUF technology, confirming its transition from labs to engineering practice and standardization.
[9] Dodis, Y. et al. Fuzzy Extractors: How to Generate Strong Keys from Biometrics and Other Noisy Data. EUROCRYPT 2004. [Peer-reviewed Article] DOI: 10.1007/978–3–540–24676–3_32 Appendix A. Mathematical foundation for compensating natural variability of bone-based PUF signals and stable key extraction without collisions.
[10] Analog Devices. Understanding the Benefits of the Physically Unclonable Function (PUF). [Engineering Review] https://www.analog.com/en/resources/technical-articles/cryptography-understanding-the-benefits-of-the-physically-unclonable-function-puf.html Part III. Practical explanation of PUF advantages over static key storage in non-volatile memory.
[11] NIST. FIPS 140–3: Security Requirements for Cryptographic Modules. 2019. [Standard] https://csrc.nist.gov/publications/detail/fips/140/3/final Part III, Appendix B. Requirements for hardware zeroization and protection of cryptographic modules against physical tampering and side-channel attacks.
[12] NIST. SP 800–63B: Digital Identity Guidelines (Authentication and Lifecycle Management). 2020. [Regulatory-Technical Document] https://csrc.nist.gov/publications/detail/sp/800-63/final Part III (suppl.), Part VI. Section 5.2.1 describes principles of authentication under duress, substantiating the module's graded response (alert signature / lockout / zeroization).
[13] IEEE Transactions on Biomedical Engineering. Intra-body Acoustic Communication Security. 2020–2023. [Scientific Publications] DOI: 10.1109/TBME.2020.3021568 (baseline issue) Part II, Part III (suppl.). Confirm protection of ultrasonic channels through bone/tissues against remote interception and jamming.
Digital Identity & Privacy Protocols
[14] W3C. Decentralized Identifiers (DID) v1.0. 2022. [W3C Standard] https://www.w3.org/TR/did-core/ Part IV. Foundation for avatar architecture, selective attribute disclosure, and graded identity without centralized registries.
[15] W3C. Verifiable Credentials Data Model v1.1. 2022. [W3C Standard] https://www.w3.org/TR/vc-data-model/ Part IV. Specification for cryptographic proofs (age, license, residency) via ZKP without transmitting raw data.
[16] Chainlink Education Hub. Zero-Knowledge Proofs: Applications & Use Cases. [Technical Review] https://chain.link/education-hub/zero-knowledge-proof-use-cases Part III. Practical examples of ZKP applications for private verification in real financial and infrastructural ecosystems.
Regulatory & Medical Certification
[17] International Organization for Standardization. ISO 13485:2016 Medical devices — Quality management systems. [International Standard] Part V, Part VI. Baseline standard for certifying the cryptographic module as an optional component of a dental implant, enabling accelerated regulatory approval.
[18] ISO. ISO 14708 (Active implantable medical devices). [Standards Series] Part II, Part V. Regulatory requirements for implants with active electronics, ensuring predictable approval and long-term biocompatibility.
[19] FDA. Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions. 2023. [Regulatory Document] https://www.fda.gov/medical-devices/digital-health-center-excellence/cybersecurity-medical-devices Part V, Part VI. Certification pathway for devices with cryptographic functions, substantiating classification of the module as a component, not a standalone medical device.
[20] European Parliament & Council. Regulation (EU) 2024/1183 (eIDAS 2). 2024. [EU Legislative Act] https://eur-lex.europa.eu/eli/reg/2024/1183/oj Part IV, Part V. Legal basis for European digital wallets, graded verification, and recognition of cryptographic signatures in e-government and finance.
[21] GDPR. Article 9: Processing of special categories of personal data. 2016. [Regulatory Document] https://gdpr-info.eu/art-9-gdpr/ Part VI. Substantiates regulatory resilience of the architecture (data never leaves the body, ZKP replaces biometric transmission) compared to centralized iris/face collection.
Worldcoin Context & Economics of Trust
[22] Rest of World. Sam Altman's Worldcoin faces mounting global regulatory pushback. 2024–2025. [Analytical Review] https://restofworld.org/2024/worldcoin-global-bans/ Interlude, Part VII. Documentation of regulatory bans and ethical debates around exchanging unique biometric data for financial incentives.
[23] Reuters. Spain, Thailand, Colombia suspend Worldcoin operations over biometric data concerns. 2024. [News Source] https://www.reuters.com/technology/worldcoin-suspends-operations-spain-2024-05-17/ Interlude. Confirmation of systemic regulatory risks of centralized biometric registries and dependence on external scanning operators.
[24] Szalvinski, P. / Industry Reports on The Architecture of Trust in Digital Economies. 2022–2024. [Analytical Reviews] Part V, Part VI. Confirmation of macroeconomic shift: value moves from attention monetization to certainty infrastructure, where trust becomes a utility layer.