If you've ever set up a personal website, tinkered with self-hosting, or even casually searched for a way to dodge a DDoS attack, you've probably encountered Cloudflare. Maybe you're even using it right now. It promises lightning-fast performance, bulletproof security, and free tools that big tech usually charges an arm and a leg for.
But here's the part no one wants to say out loud: trusting Cloudflare might be the biggest privacy gamble you didn't realize you were making.
You're Not the Customer — You're the Data Point
Let's start with the obvious truth buried in the fine print: Cloudflare is a reverse proxy. That means when you route your traffic through them — say, with Tunnels, SSL, or DDoS protection — they decrypt your HTTPS traffic to inspect and forward it. They have to. That's how the service works.
So yes, they can see your traffic. Full stop.
Most users assume HTTPS protects everything — it doesn't when your TLS is terminated at a third-party edge server. When you use Cloudflare Tunnels or their reverse proxy services, the encryption stops there, and resumes afterward. That in-between moment? It belongs entirely to Cloudflare.
Even with "Full Strict" SSL, the myth that your traffic is end-to-end encrypted and invisible to middlemen is just that: a myth. Cloudflare terminates your connection. You gave them the keys.
"But They Wouldn't Do Anything With It… Right?"
Here's where the conversation gets murky. Technically, no, there's no public record of Cloudflare maliciously snooping through user data. There's also no proof they've refused to cooperate when pressured by governments with warrants — or worse, secret letters.
They're a U.S.-based company. That means they're subject to U.S. law, which includes compliance with the Foreign Intelligence Surveillance Act (FISA) and potential cooperation with agencies like the NSA. If the government comes knocking, do you think they'll blow up their multi-billion dollar business to protect your homelab's Jellyfin instance?
Spoiler: they won't.
This isn't paranoia. It's pragmatism. Cloudflare, like every other tech company, exists to serve its shareholders. The data they can access — even if only temporarily — has intrinsic value. And while their business model doesn't currently rely on monetizing that data directly, data visibility is a strategic asset, not a liability.
Centralization: The Real Threat Lurking in Plain Sight
It's not just about whether Cloudflare is snooping on you. It's about what happens when one company becomes the internet's middleman.
As of 2024, more than 30% of all internet traffic passes through Cloudflare's infrastructure. That's not hyperbole — it's a known statistic in tech circles. If one company can see a third of the world's web requests, that's not resilience. That's a chokehold.
Imagine if a single ISP, or a single DNS provider, could flip a switch and disrupt half the internet. We freak out about AWS going down for two hours — now imagine that with your site, your traffic, and your private data being quietly filtered through a corporate-owned machine.
That's not how the internet was supposed to work.
Your Privacy Depends on Who You Trust — And You've Outsourced It
Cloudflare doesn't just provide services. It asks you to trust them, implicitly. And when you hand over the keys to your digital kingdom — through SSL termination, DNS management, or reverse tunneling — you're making a bet.
Here's the kicker: most users don't even realize they've made that bet.
They set up Cloudflare Tunnel because it's easy. It's free. It works. But beneath the simplicity is a fundamental compromise: you are giving up sovereignty over your data, even if only momentarily. And for privacy-conscious users, that should be a wake-up call.
Even services like Vaultwarden (a self-hosted Bitwarden alternative) aren't immune. While it encrypts vault data client-side, the login process still involves credentials transmitted to the server. If your server is behind a Cloudflare tunnel? Guess who's in the middle of that connection.
Yes — the credentials are typically hashed, and yes, it's unlikely Cloudflare is combing through your logins. But can they? Technically, yes.
"Eventually, You Have to Trust Someone" — But Should It Be Them?
This is the most cited defense for staying with Cloudflare: "You have to trust someone eventually."
It's not wrong. But it's incomplete.
There's a difference between informed trust and blind convenience. Trusting your VPS provider or your DNS registrar doesn't mean letting them MITM your encrypted connections. Trusting Tailscale for mesh VPN routing isn't the same as terminating your traffic on Cloudflare's edge servers.
Cloudflare is in the path. They're not just facilitating the connection — they're mediating it. That's a distinction that matters.
And yes, alternatives like Tailscale (or hosting your own WireGuard tunnels) come with complexity. But they don't force you to give up visibility and control. You can self-host their coordination layer (via Headscale), audit the open-source clients, and control your own keys.
That's what real self-hosting is supposed to be about: ownership. Autonomy. Privacy.
If It's Free, You're the Product (Yes, Still)
Let's get real: no one gives you global edge caching, DDoS protection, and SSL management for free out of the kindness of their hearts.
Cloudflare's free plan is a lead generation funnel. Your data — even just the metadata about what services you're running, what protocols you're tunneling, and when you're active — is useful. It paints a picture. It creates behavioral profiles. It trains machine learning models. Even if anonymized, it's still monetizable.
And if that weren't enough, it also creates a network effect: you get comfy in the Cloudflare ecosystem. So comfy that eventually, when your homelab grows into a side hustle, you start paying — and now you're locked in.
So… Should You Panic?
Not necessarily.
If you're using Cloudflare to host static sites, simple projects, or front-end content that's already public — the tradeoff might be acceptable. If you know what they can access and you're okay with that, cool. Calculated risks are fine. Blind trust is not.
But if you're running something sensitive — a password manager, a private analytics dashboard, a zero-trust network gateway — and you're using Cloudflare Tunnels or their SSL termination? You owe it to yourself to pause. Audit. Rethink.
There are alternatives. And you don't need to throw everything out. But the shocking truth is this:
Cloudflare's convenience hides a critical truth — they're not just serving your content. They're sitting between you and your users, quietly collecting, observing, and routing the very essence of your digital presence.
What You Can Do Right Now
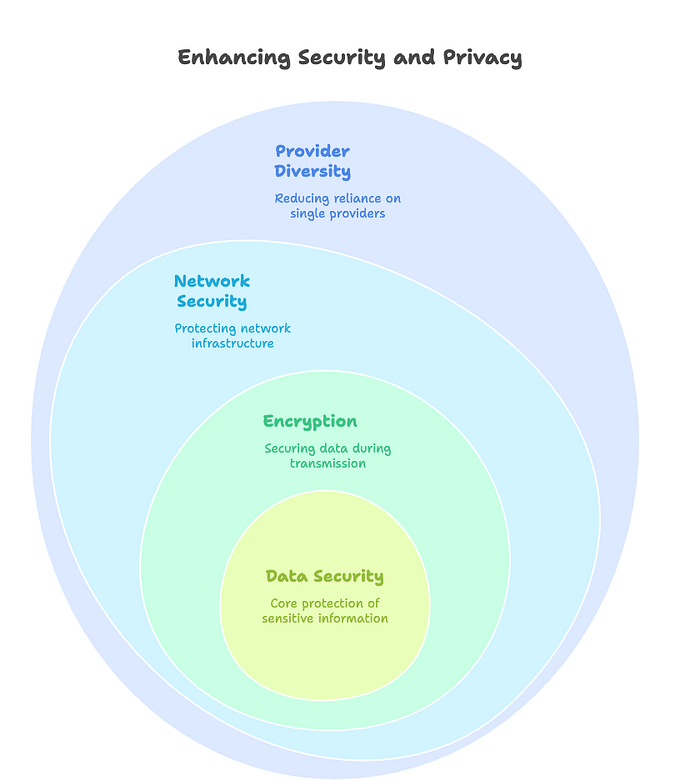
- Avoid putting sensitive apps behind Cloudflare Tunnels. Use Tailscale or WireGuard instead.
- Encrypt data on the client side before transmission. Services like Passbolt do this well.
- Use Full (Strict) SSL, but understand its limitations.
- Host your own DNS or use a privacy-first provider like ns1 or NextDNS.
- Keep your infrastructure modular. Don't rely on one provider for everything.
The internet was built on decentralization. And somewhere along the way, we traded that ideal for convenience, comfort, and corporate safety nets.
Cloudflare isn't evil. But that's not the point.
The real question is: do you trust them with your privacy?
And more importantly — should you?
