This article shows a quick and easy way to give non-admin (cluster-wise) k8s access to engineers. We achieve that by giving admin role on a namespace and generating a kubeconfig file that has access to a service account.
The steps consists of
- Creating a namespace
- Creating a token for the default service account
- Role-binding admin cluster role of the namespace to the service account
- Constructing a kubeconfig file
Environment & Requirements
Here, we will create user1ns namespace. First of all, we need a working Kubernetes cluster. Such one can be deployed by the steps explained here. We also assume to have admin access to it.
1. Namespace Creation
---
apiVersion: v1
kind: Namespace
metadata:
name: user1ns
labels:
name: userspaceWe will apply this yaml file to create user1ns namespace.
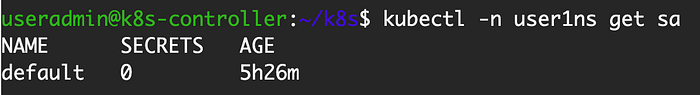
kubectl apply -f user1ns.yamlOnce it is created, default service account will be automatically created.
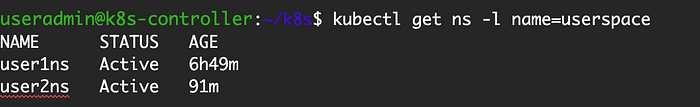
Please note that we add a label to the namespace so that we can list all the namespaces that are created in this manner.
2. Token Creation
---
apiVersion: v1
kind: Secret
metadata:
namespace: user1ns
name: default.service-account-token
annotations:
kubernetes.io/service-account.name: default
type: kubernetes.io/service-account-tokenOnce this secret is created, we can extract two properties (ca and token). They will be used for constructing a kubeconfig file later. The commands to create the secret and extract these fields from it are shown below.
kubectl apply -f user1ns-default-token.yaml
kubectl get secret -n user1ns default.service-account-token -o jsonpath='{.data.ca\.crt}'
kubectl get secret -n user1ns default.service-account-token -o jsonpath='{.data.token}' | base64 -d3. RoleBinding of admin ClusterRole to namespace
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
namespace: user1ns
name: user1ns-default-admin
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: admin
subjects:
- kind: ServiceAccount
namespace: user1ns
name: defaultThis role binding assigns admin ClusterRole to the default service account in user1ns namespace. The description of this cluster role can be found here.
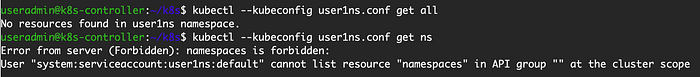
kubectl apply -f user1ns-rolebinding.yaml4. Constructing kubeconfig file for Service Account
The following is a template for kubeconfig file that uses the default service account in a namespace.
apiVersion: v1
kind: Config
preferences: {}
clusters:
- name: cluster.local
cluster:
certificate-authority-data: {{CA}}
server: {{SERVER}}
users:
- name: user1ns
user:
token: {{TOKEN}}
contexts:
- name: user1ns.cluster.local
context:
cluster: cluster.local
user: user1ns
namespace: user1ns
current-context: user1ns.cluster.localThe {{CA}} and {{TOKEN}} are the ones extracted in the token creation step. Assuming that we are using admin config from the kubespray deployment, the {{SERVER}} can be extracted using this command. Please note that the server information can be found in any working kubeconfig file.
kubectl config view -ojsonpath="{.clusters[0].cluster.server}"Now, we have a working kubeconfig file.
Other Kubernetes Articles
Please see the list of Kubernetes articles.

