🌍 The Mission: Scan Federal Domains
Let's be real — the internet never sleeps, and neither do government misconfigurations.
One night, I decided to cast a wide net across federal domains and subdomains. My goal? See what might pop up using only passive enumeration, automation… and a bit of sleep.
🔎 Step 1: Subdomain Harvesting Like a Pro
First, I collected a massive set of targets using multiple methods:
subfinder -d gov.xx -all -recursive -silentThen I doubled down with:
- Shodan searches, like:
hostname:.gov.xx - FOFA queries
- Classic Google Dorks, like:
site:gov.xx
📌 Target scope: Anything ending in
.gov.xx.
🧹 Step 2: Clean-Up Crew
After gathering thousands of URLs and subdomains:
- I stripped out the unnecessary paths
- Removed duplicate entries
- Consolidated everything into a clean
list.txt
Then I uploaded the final list to my server. Time for the magic.
🧪 Step 3: Launching the Scan (and Logging Off)
I set up Nuclei with some thoughtful flags:
nuclei -l list.txt -rl 10 -bs 2 -as -silent -s critical,high,medium -cloud-uploadLet's break that down:
-rl 10: Rate limit to avoid tripping firewalls-bs 2: Small Bulk size-as: Automatic Selection-s critical,high,medium: Focus on serious stuff-cloud-upload: Results Shows On The Cloud Platform
With the scanner running… I went to sleep 😴
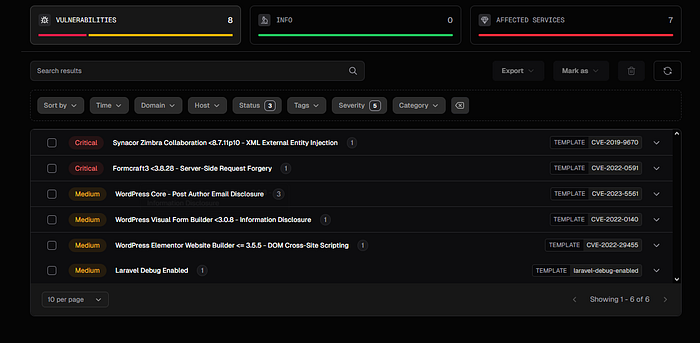
🧨 Step 4: Wake-Up Call — 8 Vulns, 2 Critical
Woke up. Checked the dashboard.
🟢 8 vulnerabilities flagged. 🔴 2 marked Critical.
Yes, while I was out dreaming, federal web assets were quietly exposing themselves — and I had the receipts.

📌 Key Takeaways
- Automation + targeting = high signal, low noise.
- Subfinder, FOFA, and dorks are still elite recon tools.
- Sleep scanning works… when your config is solid.
- Always scan ethically. Always disclose responsibly.
🧘 Final Thoughts
This wasn't a CTF. This was the real deal.
Federal domains, quietly leaking critical vulnerabilities while no one's watching.
If you're in this space:
- Know your tools.
- Respect your targets.
- Automate what you can.
- And sometimes… just hit run and go to sleep 😎
Follow for more real-world recon and vuln-hunting stories.

