Hi, this blog contains my solutions to the OSINT Industries CTF Challenges.
Disclaimer: This content is for educational purposes only.All information was obtained from publicly accessible sources, and no paid tools or unauthorised access methods were used.
TL;DR — Challenges Breakdown:
GEOINT
Find the Masked Man: Located the target using Google Maps analysis.
OSINT
DEPIX: Extracted hidden information via barcode scanning.
Holehe & the Secret Email: Used Holehe to identify the account creation date.
On the Traces of the Silk Road Black Market: Correlated Yelp data to identify Ross Ulbricht's profile and a review linked to a birthday location.
Found the Hacker: Crawled Archive.org with Waymore to recover forum posts, then pivoted from a username to an email, Twitter, and YouTube accounts.
FSB
FSB Part 1–3: Solved using publicly available data leaks.
INTERPOL
The Benarroch File: Retrieved address information from French business directories.
The Hadjej File: Identified the email address via data leak analysis.
GRU
GRU Foreign Operations: Interpreted poetic hints to map them to a famous case, then used official inquiry documents to extract related details.
EUROPOL
Operation LOCKERGOGA: Used Instagram to determine vehicle mileage.
Detailed Solutions
CHALLENGES:
· GEOINT ∘ Challenge: FIND THE MASKED MAN · OSINT ∘ Challenge # 1 DEPIX ∘ Challenge # 2 HOLEHE & THE SECRET EMAIL ∘ Challenge # 3 On the Traces of the Silk Road Black Market ∘ Challenge # 4 Found the HACKER · FSB ∘ Challenge: FSB PART 1 ∘ Challenge: FSB PART 2 ∘ Challenge: FSB PART 3 · INTERPOL ∘ Challenge # 1 The Benarroch File ∘ Challenge # 2 The Hadjej File · GRU ∘ Challenge: 3GRU FOREIGN OPERATIONS · EUROPOL ∘ Challenge: Operation LOCKERGOGA
Let's Start:
GEOINT:
Challenge: FIND THE MASKED MAN
Description:
A photograph was taken in Paris on December 3rd, 2023, around 18:00. Your mission is to identify the nearest metro station to the location where the masked man was photographed.
Context:
Investigators received an image showing a masked individual standing in a central and upscale district of Paris.
The metadata and environmental observations indicate:
- The image was taken on December 3rd, 2023
- The approximate time was 18:00 (early evening)
- The location is in Paris, within a central and upscale area
- The scene is located near the intersection of a Rue and an Avenue
Objective:
Your objective is to determine the closest metro station to the photographed location, using only the contextual and visual clues provided.
Mission:
Analyze the given information and identify the nearest Paris metro station.
Lets start:

Let's zoom to read the text

the word "JULIEN" can be read and "blue mark" and "screen" can be seen
lets search "JULIEN" on google map focusing on "intersection of a Rue and an Avenue"
I identified this shop by matching visual details from the selfie above.
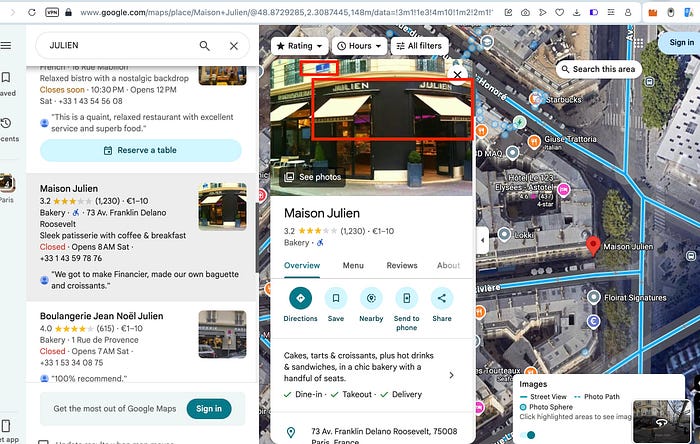
now we explore from street view:
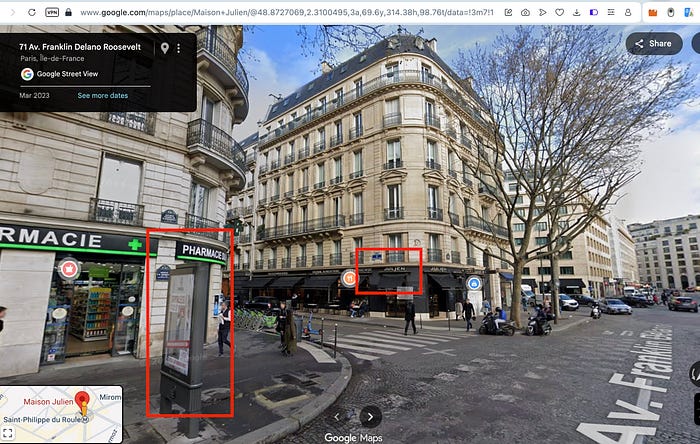
as you can see the "screen" "blue mark" and "JULIEN"
Analysing the image side by side:

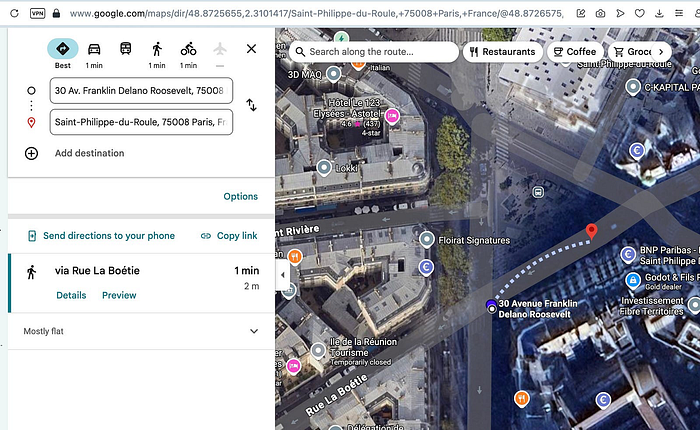
Finding the Metro Station:
as you can see the "Train" icon it shows the bus stop for the metro station:
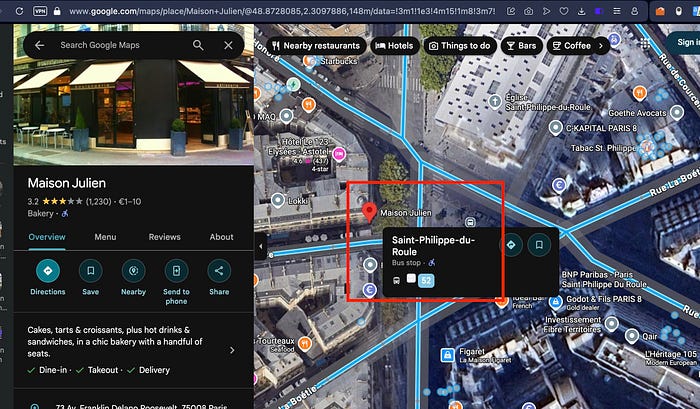
Based on the distance the nearest metro station is: Saint-Philippe-du-Roule
OSINT :
Challenge # 1 DEPIX
Target Information:
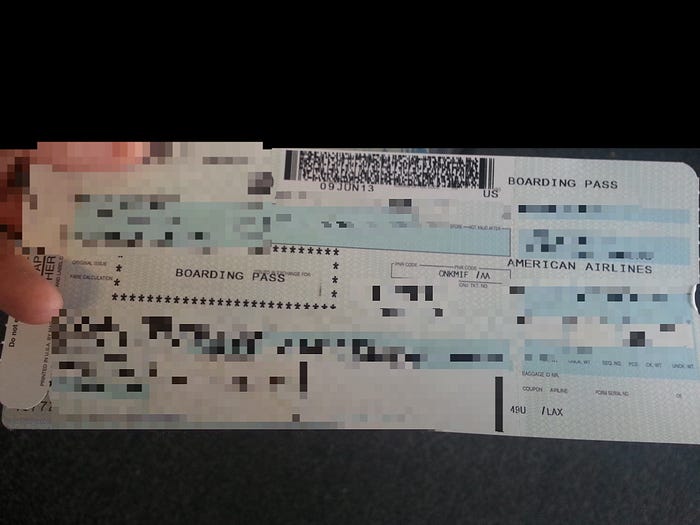
A passenger posted a photo of their flight ticket online. The ticket is heavily pixelated, but key details remain partially recoverable.
Your task is to identify:
- The passenger's first and last name
- The seat number
- The arrival airport IATA code
Let's start:
All the things are blurred but we only need this:
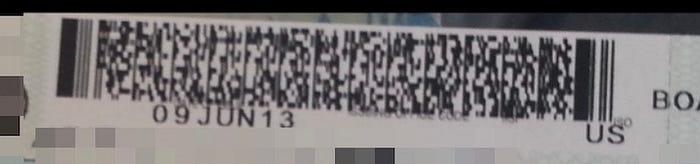
Lets scan this on this site
Lets analyse the result
M1CHEN/MICHAEL EONKMIF LAXPVGAA 0183 160F003D0120 347>118
Breakdown of the fields:
- M — Format code: "M" indicates the mandatory format for a single-leg boarding pass (most common for direct flights).
- 1 — Number of legs/segments: 1 (single flight segment).
- CHEN/MICHAEL — Passenger name: Surname "CHEN", given name "MICHAEL"
- EONKMIF — Electronic ticket indicator: "E" (electronic ticket), followed by conditional fields. "ONK" likely the operating carrier code "MIF" may be part of airline-specific data or frequent flyer info.
- LAXPVGAA — From/to airports and airline: Origin "LAX" (Los Angeles International Airport), destination "PVG" (Shanghai Pudong International Airport), operating/marketing airline "AA" (American Airlines).
- 0183 — Flight number: AA0183 (or carrier-specific numbering; American Airlines does operate routes or codeshares to PVG).
- 160 — Julian date of flight: Day 160 of the year (June 9, since 2025 is not a leap year: January 31 + February 28 + March 31 + April 30 + May 31 = 151 days, so 160 = June 9).
- F — Compartment/code (cabin class): "F" typically means First Class.
- 003D — Seat number: 003D (seat D in row 3, common in first-class cabins).
- 0120 — Sequence number: 0120 (boarding sequence or check-in order; used internally for boarding priority).
- 347>118 — Beginning of variable/conditional fields: Starts with passenger status or source of check-in (e.g., "3" often web check-in, "4" airport). The ">" separates mandatory from optional sections, followed by airline-specific item identifiers like "1" (ticket number part), "18" (additional data).
Summary of the flight details:
- Passenger — Michael Chen
- Flight — Likely American Airlines (AA) flight 183 (or codeshare) from Los Angeles (LAX) to Shanghai Pudong (PVG)
- Date — June 9 (year inferred from context, e.g., 2025)
- Cabin — First Class
- Seat — 3D
Challenge # 2 HOLEHE & THE SECRET EMAIL
Description:
You are investigating the origins of a popular OSINT tool used to pivot from email addresses to online accounts: Holehe.
Behind every tool, there is a creator — and behind that creator, there is an email address.
Your mission is to trace back the very first appearance of the creator's email address online and determine the exact date it was created.
Objective:
Using open-source intelligence only, find:
- The creator of Holehe
- The public email address used for Holehe
- The exact creation date of this email address
Let's start:
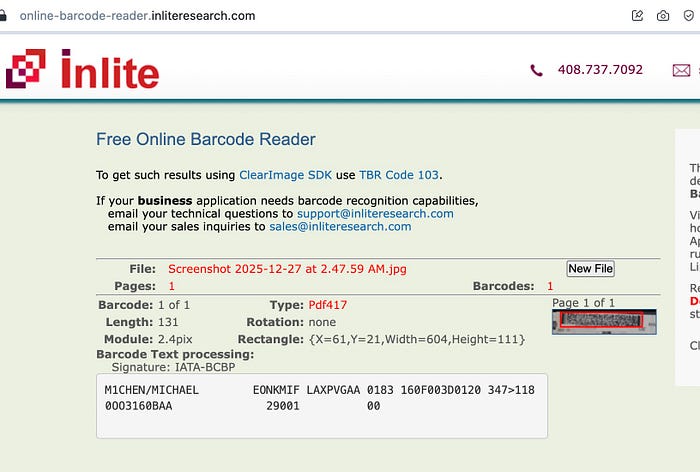
We can get the creator's eamil from his github profile:
We can use holehe on this email: megadose@protonmail
holehe:
holehe megadose@protonmail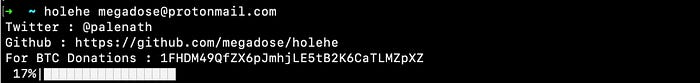
and it shows the creation date:
Creation Date: 2021–01–14
Challenge # 3 On the Traces of the Silk Road Black Market
Background:
In 2010, before his arrest, Ross Ulbricht celebrated his girlfriend's birthday at a specific location. Through careful open-source analysis of information publicly available from that period, it is possible to determine:
- The exact name of the location linked to the birthday celebration
- The girlfriend's day and month of birth, which can be inferred from contextual clues found within legal, publicly accessible sources
Objective:
- The name of the location associated with the 2010 birthday event
- The girlfriend's day and month of birth
Let's start:
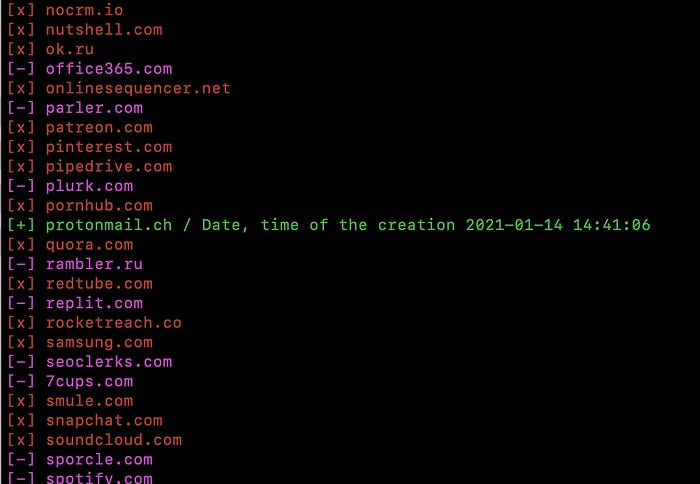
In 2010 ross's GF was "julia vie".
So let's find out her birthday
Google search shows this image uploaded on 25th sep, 2020
which means DOB is 25/09
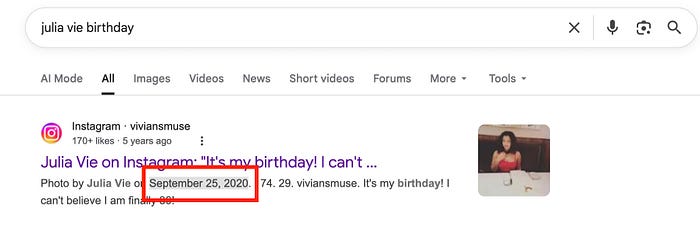
from her insta we get to know about her business:
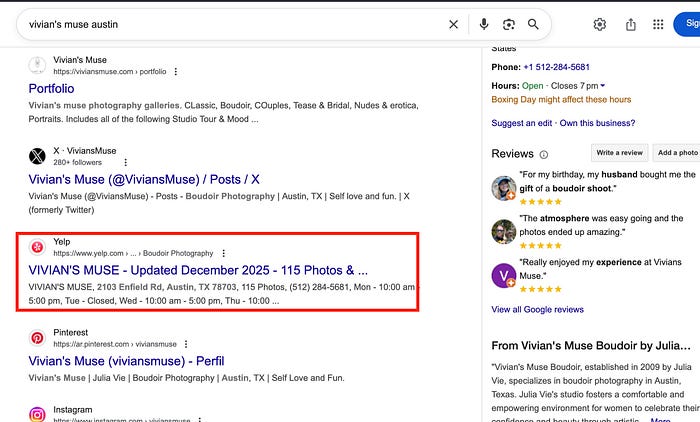
Let's explore yelp:
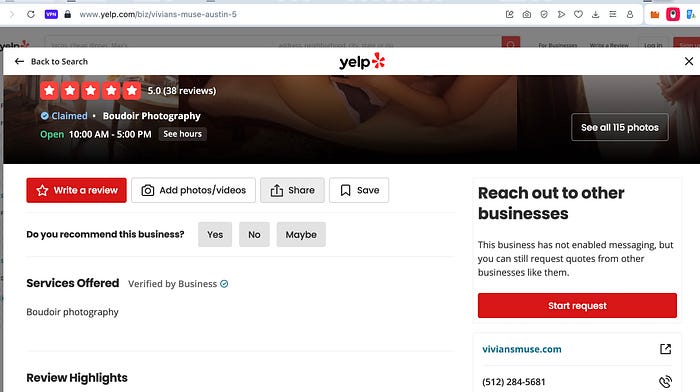
Reading Reviews by sorting as oldest:
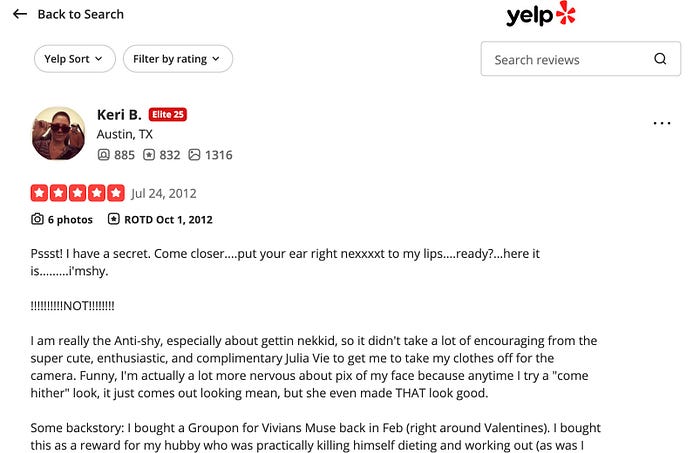
but no review from 2010 , scrolling down we see not recommended reviews:
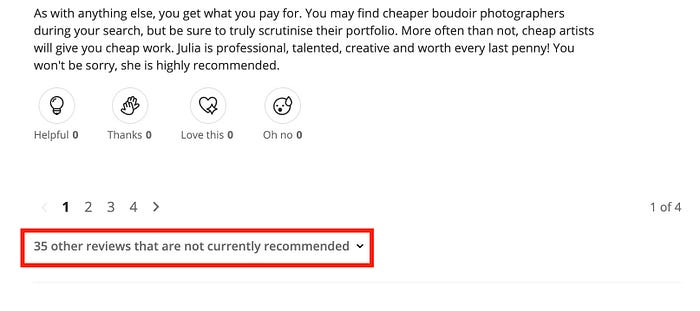
We find review by "Ross U" in 2010:
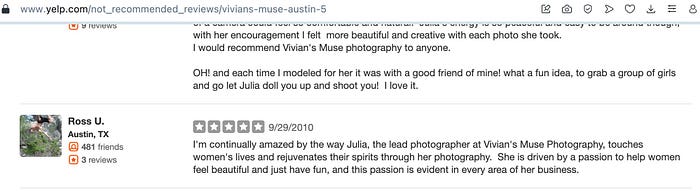
Why Reviews? Because its common to review each other business bw friends etc.
Let's use yelp "Search Friends"
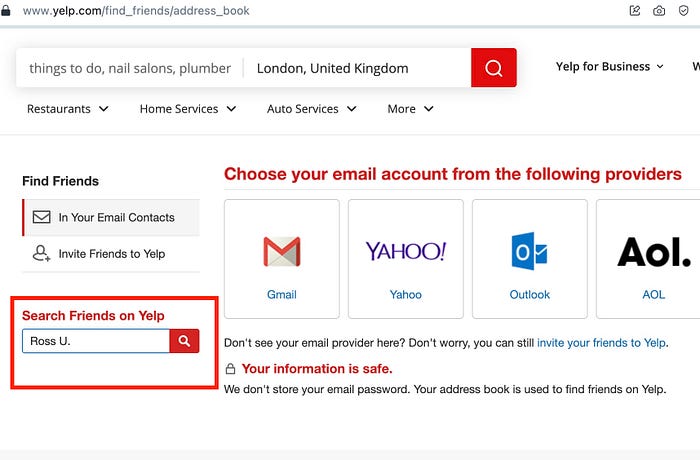
and we got his profile
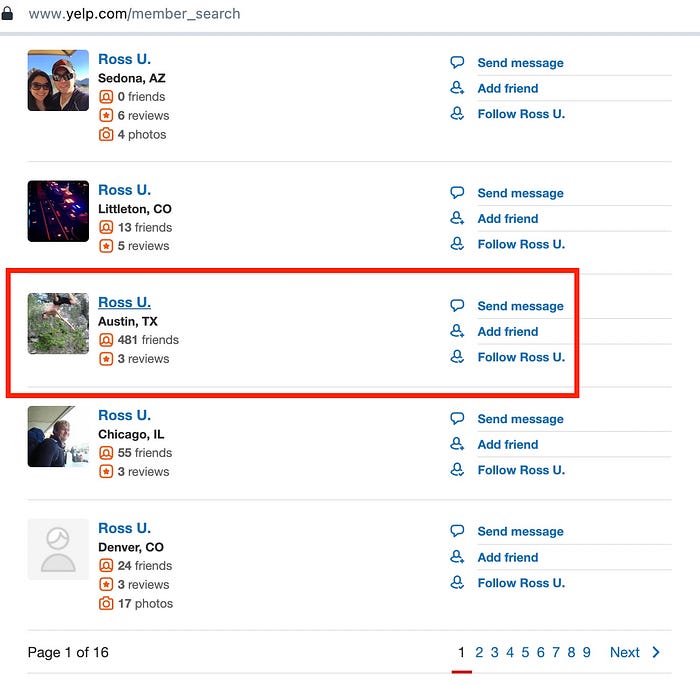
reading his reviews we got this:
DOB: 25th/09
Place: Aquarelle
Challenge # 4 Found the HACKER
Context:
Several years ago, a cybercriminal published a message on a well-known underground forum.
The individual was the author of the thread referenced below.
Thread Information:
- Thread URL: https://[REDACTED]/Thread-New-User-pass-40k-gmail-prmuim-netflix-hulu-steam-uplay-spotify
- Date: May 11, 2018–03:38 PM
- Content: Just Do it : http://[REDACTED]
Objective:
Your mission is to identify the cybercriminal behind this forum post using open-source intelligence only.
You must determine:
- The email address used by the individual. This email appears on multiple cybercrime-related forums, allowing strong attribution.
2. The individual's Twitter account
3. The country where the individual lives (Country name must be provided in English.)
4. The individual's first name
Let's start:
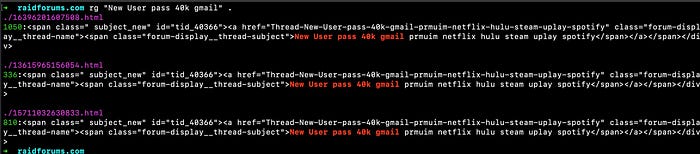
So based on the format and the date it can be determind that the forum is "RaidForums" because it was very famous in 2018 and until its takedown….
- OSINT for EMAIL:
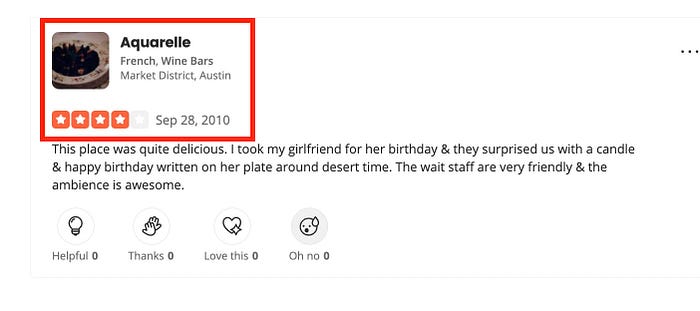
searching for the link https://raidforums.com/Thread-New-User-pass-40k-gmail-prmuim-netflix-hulu-steam-uplay-spotify
on wayback machine didn't bring any results:
but the forum itself has been archived many times:
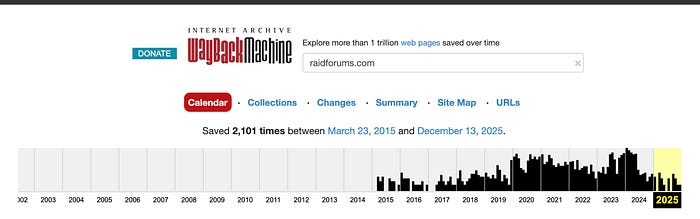
So let's try to collect all the urls using waymore tool:
Why Waymore? Becuase it is fast and it also crawls urls from other sources like urlscan, alienvault etc…
waymore -i raidforums.com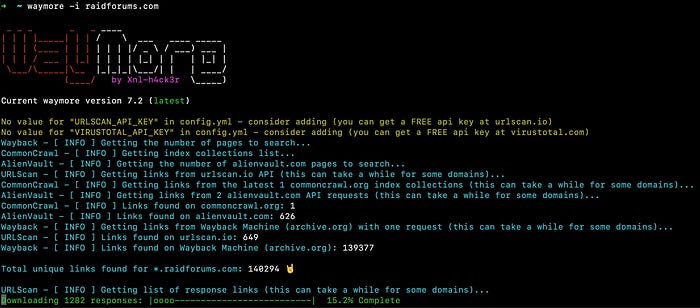
after it has collected all the urls you will see waymore.txt which will have all the urls.
searching for the thread in waymore.txt
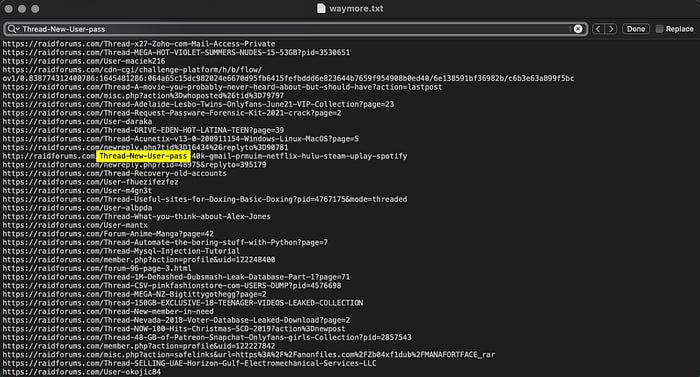
Now its verified that the thread exists and it's from raidforums.
waymore also downloads the urls which can be found in ~/waymore/raidforums.com
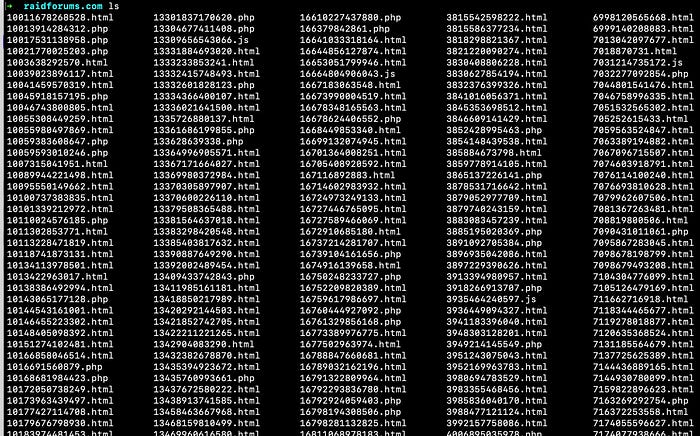
ripgrep for the thread in these files:
opening the file locally:
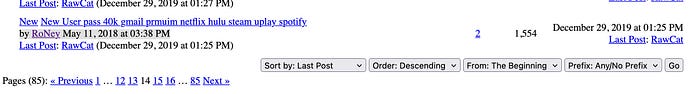
and on the wayback:
and we can see the thread author name which is "RoNey"
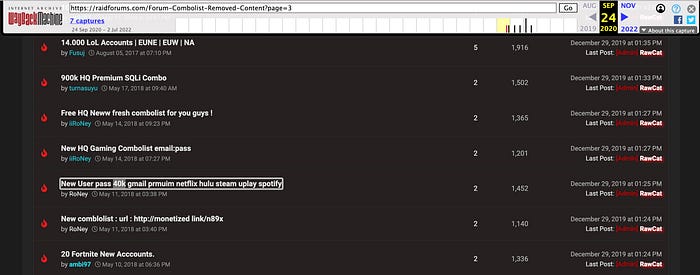
So in 2023 somebody had leaked the user database of raidforums searching for this username can lead us to his email.
Searching for "RoNey" in the db show his gmail "roneyads1@gmail.com"
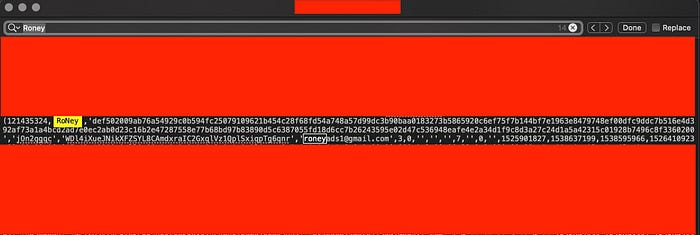
Email: roneyads1@gmail.com
2. OSINT for Twitter account:
Searching for his gmail in leak dbs leads to his username:
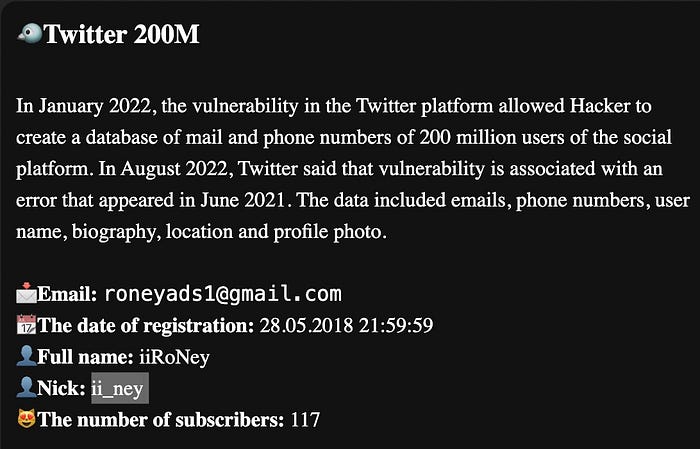
Verifying:
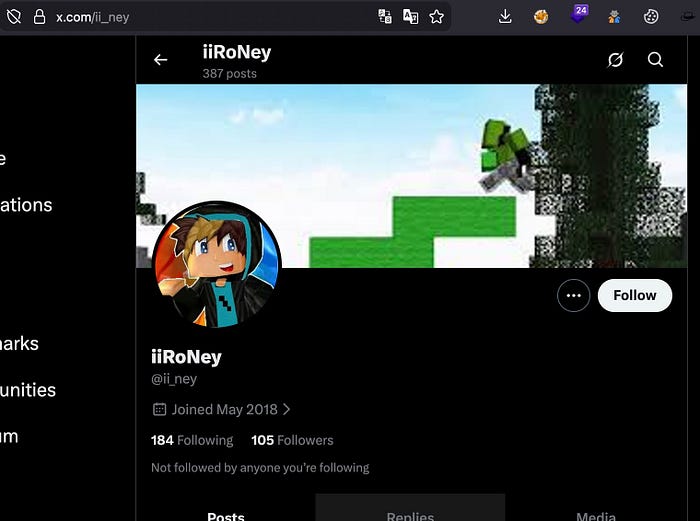
X: ii_ney
3 & 4. OSINT to find Country and FirstName:
google search leads us to his youtube channel:
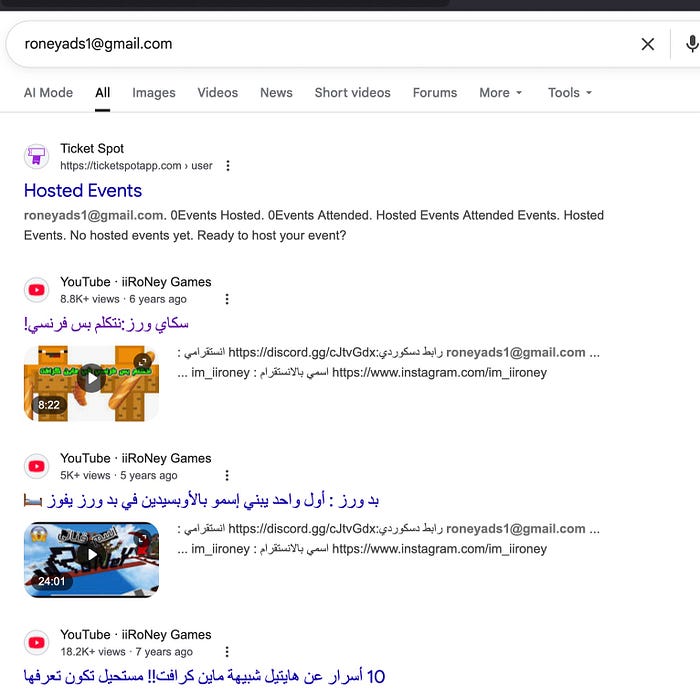
Channel's About Section:
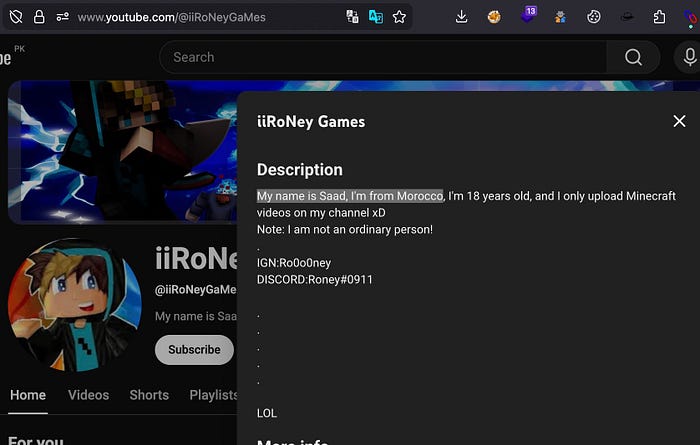
Name: Saad
Country: Morocco
FSB
Challenge: FSB PART 1
Context:
A historical dataset linked to an FSB-related leak contains partial civil information. Only the individual's identity is visible. The date of birth is missing.
Known Information:
- Full name: КОВЖАРОВА ЕЛЕНА АЛЕКСАНДРОВНА
- Gender: Female
Objective:
Using open-source intelligence methods, determine the date of birth of the individual.
Let's start:
КОВЖАРОВА ЕЛЕНА АЛЕКСАНДРОВНА is KOVZHAROVA ELENA ALEKSANDROVNA in english.
Searching for her name shows 3 results and 1 has an date
Let's explore this:
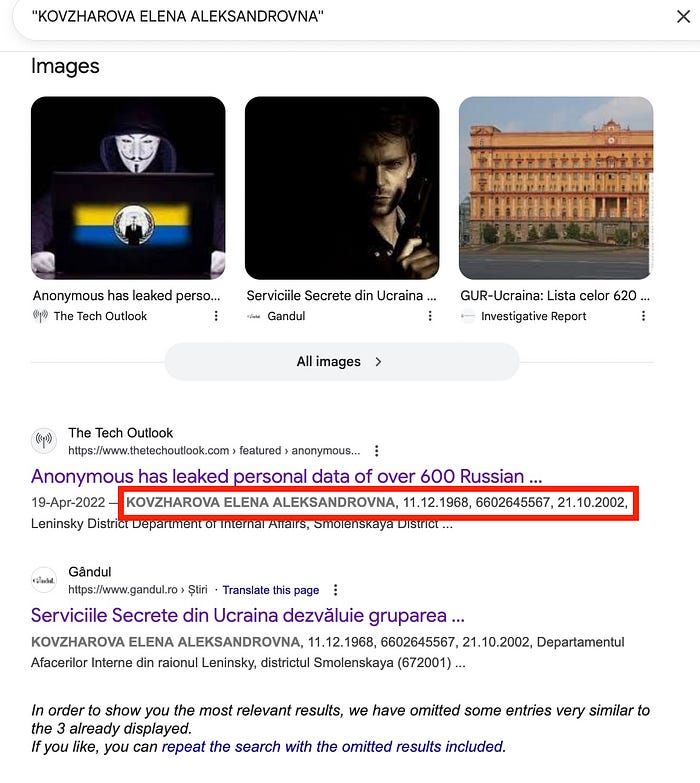
It shows her DOB and other things:
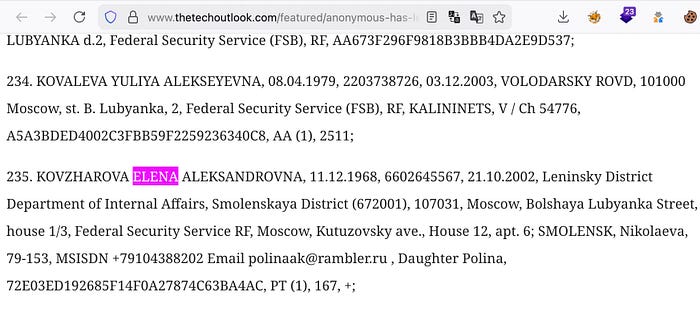
DOB: 11/12/1968
Challenge: FSB PART 2
Context:
A separate dataset references the same individual but contains only a digital contact identifier. Other personal identifiers were removed.
Known Information:
- Email address: polinaak@rambler.ru
This email address appears across multiple historical data sources.
Objective:
Using passive OSINT correlation, identify the national social security identifier (SNILS) associated with the individual.
Let's start:
Searching for polinaak@rambler.ru in the data leaks shows 2 hits:
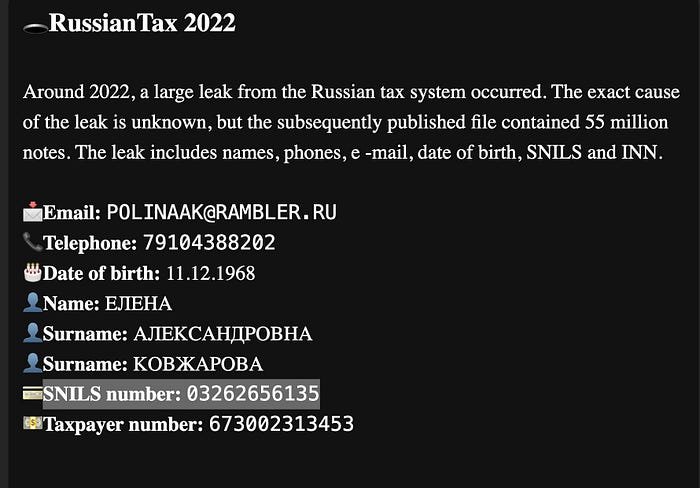
and
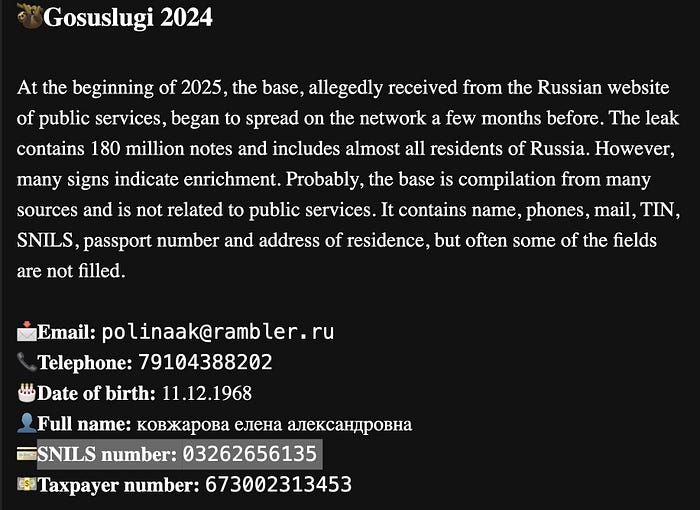
SNILS: 03262656135
Challenge: FSB PART 3
Context:
Archived online records indicate that personal identifiers were reused across social platforms. The profile itself is not directly named.
Known Information:
- Email address: polinaak@rambler.ru
- Phone number: +7 910 438 8202
Objective:
Identify the VK social network profile historically associated with these identifiers.
Let's start:
Searching for polinaak@rambler.ru in the data leaks shows this:
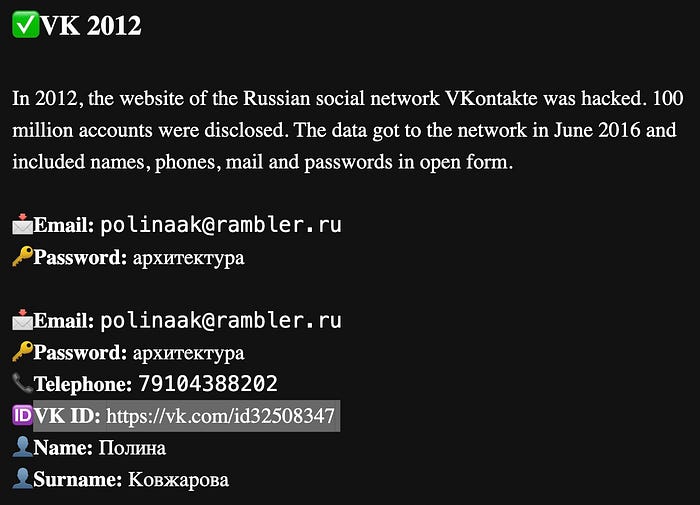
VKID: https://vk.com/id32508347
INTERPOL
Challenge # 1 The Benarroch File
Target Information:
Name: BENARROCH, INONE Date of birth: 19/05/1978 Age: 47 Country link: Israel, France
Objective:
Using only legal open-source intelligence methods, identify the last known address of the individual in the year 2015
Let's start:
"Inone BENARROCH" 2015 on google:
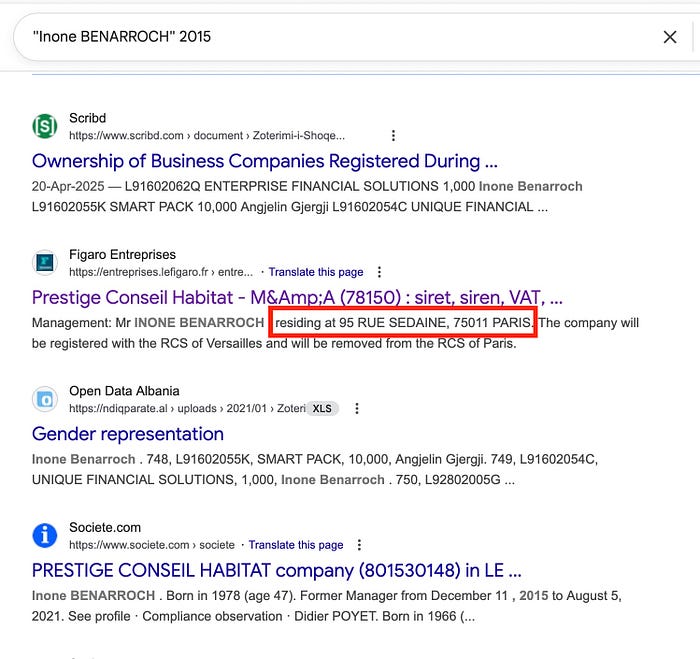
"residing at …." .So this site is worth checking…
Scrolling the site leads us to the "Free Document" section and it has some documents from the year 2015.
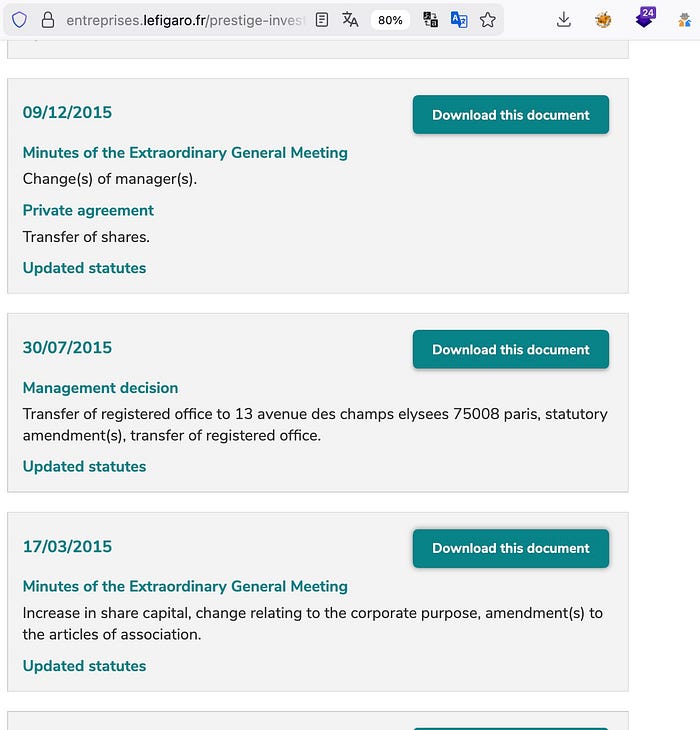
Let's download the above files.
1 file contains his name with address:
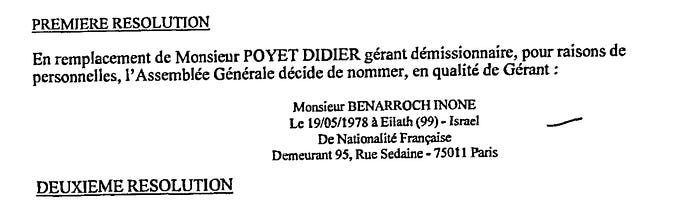
Address: Demeurant 95, Rue Sedaine — 75011 Paris
Challenge # 2 The Hadjej File
Target Information:
Name: Olivier HADJEJ Date of birth: 17/07/1967 Countries linked: France, Israel
Objective:
Using legal open-source intelligence methods, identify one email address that can be reasonably linked to the individual named above.
Let's start:
So searching for his name "Olivier HADJEJ" in the leaks
which gives us his email which:
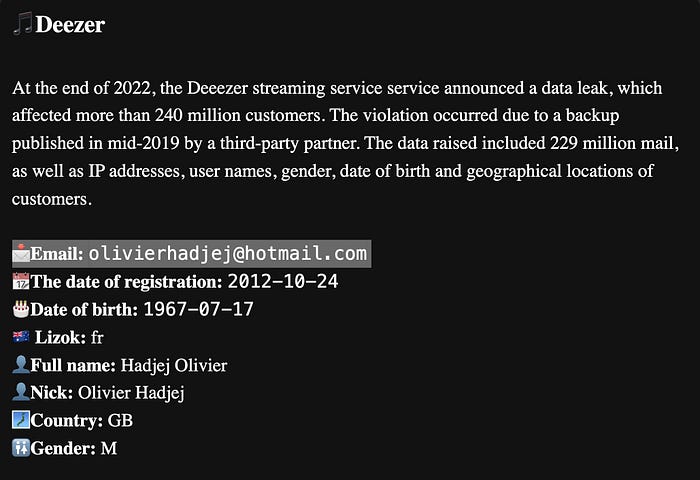
Email: olivierhadjej@hotmail.com
GRU
Challenge: 3GRU FOREIGN OPERATIONS
A fragment of an old poem has surfaced in an online dead-drop allegedly used by a former Russian intelligence agent. It is connected to a high-profile defection case, but nothing in the text is explicit.
Despite the ambiguity, the fragment contains enough indirect indicators — linguistic patterns, temporal references, and operational clues — to reconstruct the event.
Objectives
Using only legal open-source intelligence (OSINT) methods, identify:
- The NAME and SURNAME of the FSB agent who defected
- The exact date the covert operation took place (DD/MM/YYYY)
- The exact place of the operation (2 words)
- Shortly after the operation, a suspicious dark blue vehicle was reportedly seen parked near the entrance. Identify the registration plate of the vehicle.
Let's start:
An file named "pdf" is provided which can be viewed by adding extension pdf.pdf
Analysing its metadata:
exiftool pdf.pdf
ExifTool Version Number : 12.30
File Name : pdf.pdf
Directory : .
File Size : 1837 KiB
File Modification Date/Time : 2025:12:15 14:49:41+05:00
File Access Date/Time : 2025:12:15 15:25:36+05:00
File Inode Change Date/Time : 2025:12:15 15:25:36+05:00
File Permissions : -rw-r--r--
File Type : PDF
File Type Extension : pdf
MIME Type : application/pdf
Linearized : No
Page Count : 1
PDF Version : 1.4
Tagged PDF : Yes
XMP Toolkit : Image::ExifTool 13.30
Creator :Main Intelligence Directorate (GRU)
Subject : Don't waste your time on metadata. There's nothing there.
Title : «"TOP SECRET - For overseas operations"
Author : Management 54777
Producer : Main Intelligence Directorate (GRU)
Create Date : 2006:10:30 00:00:00
Modify Date : 2006:10:30 00:00:00
Keywords : operational, materials; disinformation; active, measures; special operationsCreation date is 2006:10:30
Correlation with real‑world timeline:
Late October 2006 aligns with one major foreign intelligence event:
- Former FSB
- Public defector and critic
- Poisoned in London (capital hint is also in the Poem)
- Incident date: 01/11/2006
- Death: 23/11/2006 (Morse Code also hints at "MAKE HIM PAY" meaning revenge)
The PDF date (30/10/2006) is 48 hours before operation.
The Morse code also states: "USE YOUR HEAD AND YOUR TRAINING" which hints at that the suspect tried to poison him earlier:
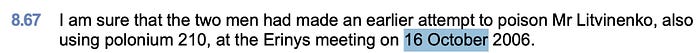
Let's investigate this Case:
Now at this point we know the NAME and SURNAME. Let's find other required information:
2. The exact date the covert operation took place (DD/MM/YYYY)
Although it is a known fact that on November 1, 2006 — The successful poisoning occurred during a meeting at the Millennium Hotel's Pine Bar in London, where Litvinenko drank tea laced with polonium-210.
Let's verify it ourself:
Searching for the inquiry leads us to the The Litvinenko Inquiry by UK GOV
They had meeting in Pine Bar:
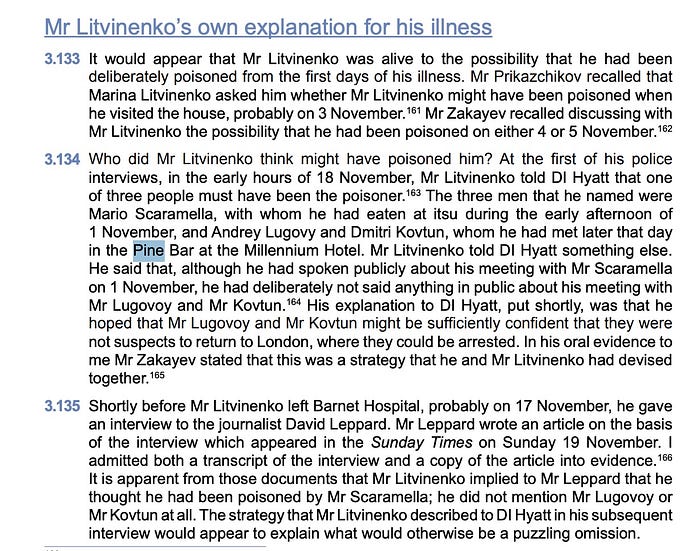
Receipt from pine bar which mentions date, time and "TEA" etc..
DATE: 01/11/2006
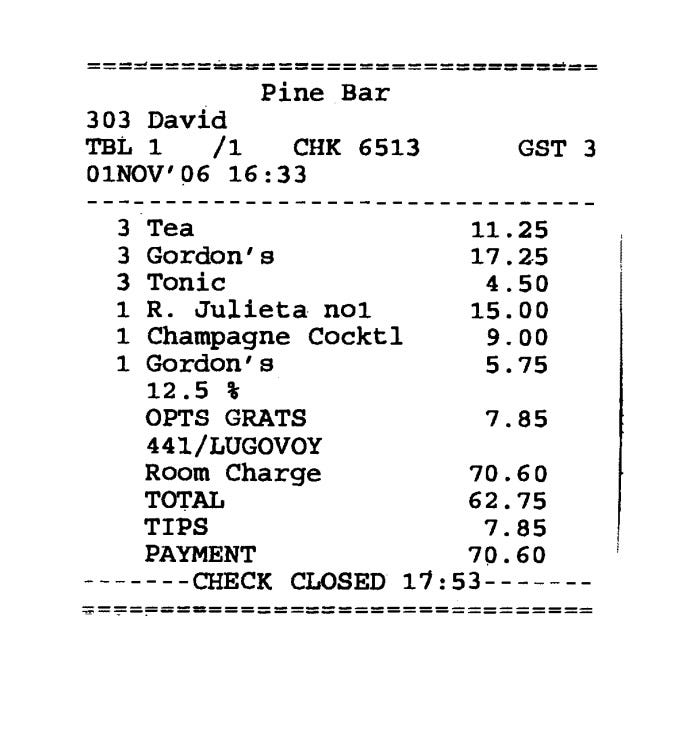
3. Location: PINE BAR
4. suspicious dark blue vehicle:
This is where the challenge became difficult, as I could not find any "suspicious dark blue vehicle" that arrived shortly after the operation.
The only blue car visible in the CCTV footage had a very blurred license plate, and the other vehicles listed in the Radiation Schedules were not accepted by the challenge.
Eventually, the correct vehicle turned out to be one I had initially dismissed, as it dated back to 2008.
However, a partial license plate was visible. By correlating the readable digits, it was possible to reconstruct the plate:
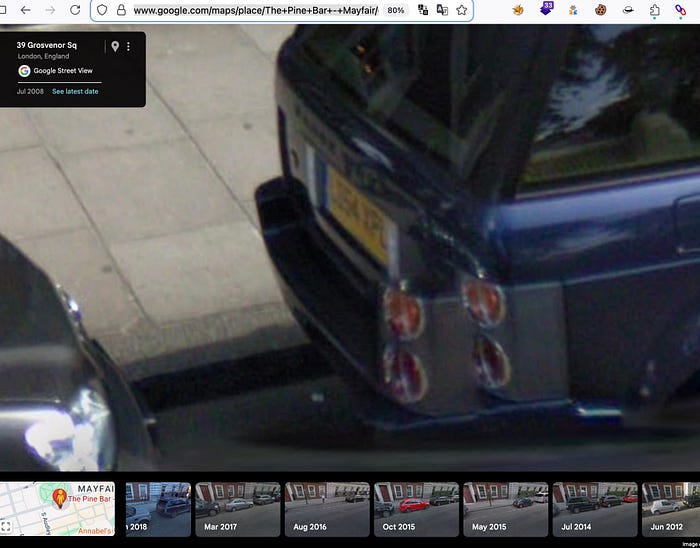


The only missing digit looks like: B, 8 , D ,0
Guessing above digits with L_54 XPL. I got this and it matches the colour and make
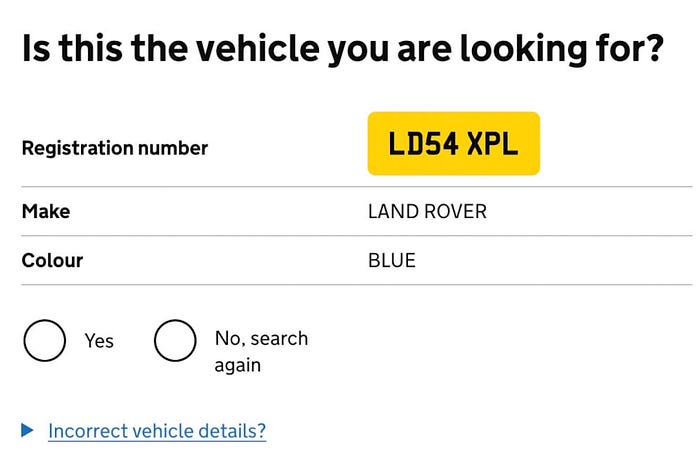
!suspicious dark blue vehicle: LD54XPL
EUROPOL
Challenge: Operation LOCKERGOGA
Target Information:
- Name: TYMOSHCHUK (ТИМОЩУК), Volodymyr Viktorovych (Володимир Вікторович)
- Date of birth: October 2, 1996 (29 years old)
- Countries linked: France, Ukraine
Objective:
Using legal open-source intelligence methods, identify:
- the licence plate of the vehicle linked to the individual
- its brand
- model
- year of manufacture
- last known mileage
Let's start:
"Volodymyr Tymoshchuk" AND "Car" searching on Google
Result shows an link with an License plate so it's worth exploring
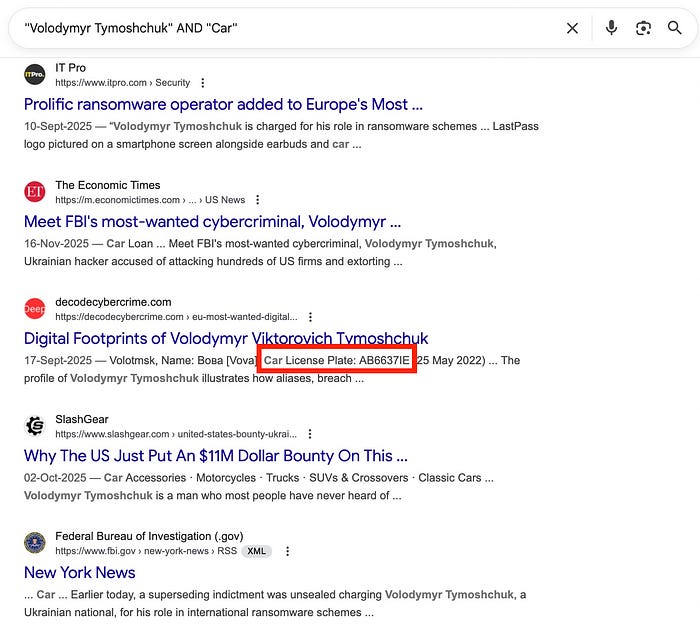
- we see the car license plate: AB6637IE
Exploring above blog:
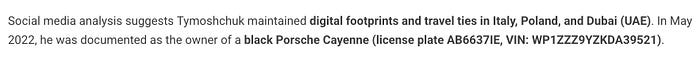
Now we also have the VIN: WP1ZZZ9YZKDA39521
And INSTA profile has the Car image that confirms the license plate:
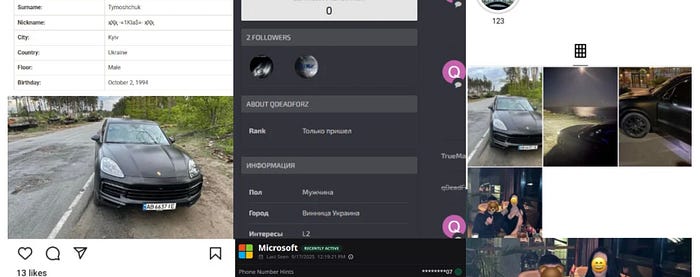
We can use the VIN to find more details about the car
Using api from https://www.vehicleregistrationapi. com as it has Precise Data.
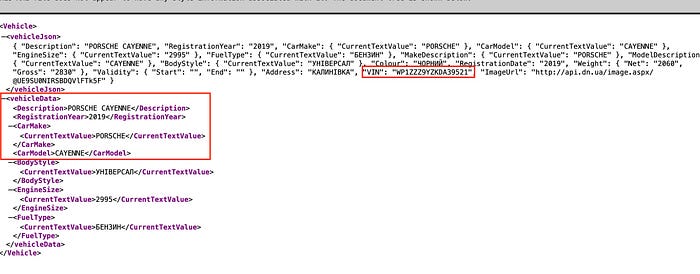
2. BRAND: PORSCHE
3. Model: CAYENNE
4. YEAR: 2019
Now let's find out the milage:

Let's download this "highlight" to see digits clearly
Viewing the story frame by frame:
5 . we can now clearly see the mileage: 36921KM
Conclusion:
Overall, this CTF emphasised the importance of methodology, patience, and attention to detail in OSINT investigations. The correct answers often came from re-evaluating assumptions and correlating small pieces of publicly available information. OSINT Industries delivered a challenging and realistic set of scenarios that effectively reinforced real-world OSINT workflows.
