Background
I previously completed the TCM Security PNPT AD pentest exam in 2022, so I brought some AD fundamentals into this challenge. I bought the C-ADPenXv2 in April 2025 during an initial release sale (90% off) after reviewing the syllabus — it looked like a realistic, complex AD pentest lab.

Exam format
The exam is flag-based: 14 tasks, 7 hours total. You get one free retake if you fail.
Passing score is 60%; scoring above 75% earns "with merit."
Test access is provided via a VPN link by email and you launch the exam through the SpeedExam candidate portal.
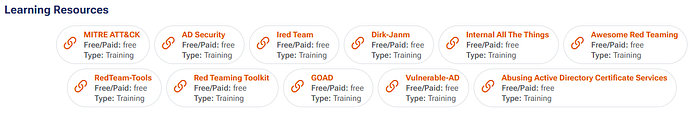
The SecOps Group does not provide study materials — they only list references on pentestingexam.com.
1st attempt
I underestimated the exam and underprepared. Endpoint protection prevented the lateral movement techniques I'd used previously, so I failed my first attempt. That was a wake-up call.
What matters: methodology and defense evasion.
This exam requires solid methodology and explicit defense-evasion techniques. If you expect to just run psexec, secretdump, or Mimikatz without evasion, you'll likely be blocked. Strengthen your AD pentest methodology before you book the exam.
Study checklist (recommended)
- Master AD enumeration methodology (this exam made me appreciate NetExec).
- Learn to read and analyze BloodHound — it's essential for AD engagements.
- Build a structured privilege-escalation approach (local admin → Domain Admin).
- Practice defense evasion — endpoints will often block naive payloads.
- Review the full range of AD attacks (Pass-the-Hash, Kerberos abuses, Trust Abuse, etc.).
2nd attempt and outcome
I dedicated time to studying these areas and practicing under time pressure. In October 2025 I retook the exam. I was able to compromise almost all endpoints this time, but I ran out of time on the final flag (only 1 minute left). Despite that, my overall score was a pass.

Impressions and score
The exam is realistic and well-designed — you start without credentials, no assumed breach. The lab was stable, though I did encounter two tasks where I couldn't obtain flags even after gaining administrative access — that's an area they could improve.
Overall rating: 8/10.
Thanks for reading — if you're preparing for C-ADPenXv2 and want notes or practice ideas, drop a comment and I'll share what helped me most.
References
- The Hacker Recipes — Practical recipes and walkthroughs for offensive tools and techniques. https://www.thehacker.recipes/
- InternalAllTheThings (swisskyrepo) — Extensive collection of internal penetration-testing resources, cheatsheets, and scripts. https://swisskyrepo.github.io/InternalAllTheThings/
- RedTeam-Tools (A-poc) — GitHub repository listing offensive/Red Team tooling and scripts. https://github.com/A-poc/RedTeam-Tools
- ADSecurity (Sean Metcalf & community) — Deep-dive articles, techniques, and guidance focused on Active Directory security and attacks. https://adsecurity.org/
- vulnerable-AD (safebuffer) — Intentionally vulnerable Active Directory lab environment (GitHub) for practice and testing. https://github.com/safebuffer/vulnerable-AD
- GOAD (Orange Cyberdefense) — Guide to Offensive Active Directory (GOAD): methodologies, attack vectors, and practical guidance. https://orange-cyberdefense.github.io/GOAD/
