🛡 Cyber Threat Intelligence Report
Report ID: AMOS-MAR-2026–001 Malware Family: Atomic Stealer (AMOS) Threat Actor: Unknown (Slavic-origin / "xxxblyat" Identifier) Primary Objective: Financial Theft & Long-term RAT (Remote Access Trojan) Access
Primary Target: macOS (Intel/Apple Silicon) Campaign Identifier: xxxblyat / b45401ac3c614f06b5daef4ab6749b34
1. Executive Summary
Analysis of a multi-stage infection chain originating from a "ClickFix" social engineering lure. The payload is a sophisticated AppleScript-based variant of Atomic Stealer (AMOS). Beyond standard credential theft, this variant implements a Persistent RAT (Remote Access Trojan) capability, allowing for arbitrary shell execution and SOCKS5 proxying. Found in a
"Typosquatting" website which was "ptython[.]com"
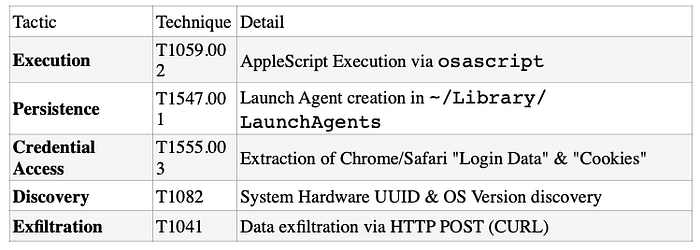
2. Technical Analysis (TTPs)
Initial Access & Execution
- Vector: Social Engineering (Fake browser update/error).
- Execution: A Base64-encoded shell command executed via bash.
- Payload: An obfuscated AppleScript (osascript) that utilizes numeric function names and string reversal to evade static detection.
Data Harvesting (The "Target Matrix")
- The malware performs a recursive scan of the user's home directory, targeting high-value financial and session data while explicitly ignoring "noise" directories (e.g., Cache, GPUCache).
- Browsers: Chrome, Edge, Brave, Opera, Vivaldi, and Waterfox.
- Cold Wallets: Exodus, Atomic, Coinomi, Electrum, Bitcoin Core, Monero (Wallets), and Wasabi.
- Hardware Wallet Apps: Trezor Suite, Ledger Live (Desktop versions).
- System Files: login.keychain-db (Targets the macOS Keychain for system-wide credentials).
- File Scavenger: Automated search for .txt, .seed, .kdbx, and .pdf containing sensitive strings.
Persistence & C2 (Command & Control.
Unlike older versions of AMOS, this variant establishes long-term persistence:
Persistence: Installs a LaunchAgent (.plist) with KeepAlive set to true. C2 Gateway: hxxp[://]217[.]119[.]139[.]117/api/v1/bot/
RAT Capabilities:
◦ doshell: Remote command execution. ◦ enablesocks5: Pivoting/Proxying traffic through the victim's IP.
◦ repeat: Self-updating mechanism via remote bash injection.
3. Indicators of Compromise (IOCs):
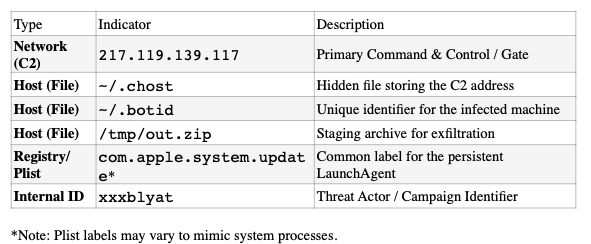
4. Domain Lookup & Infrastructure The malware infrastructure is linked to Galeon LLC, a hosting provider based in Russia.
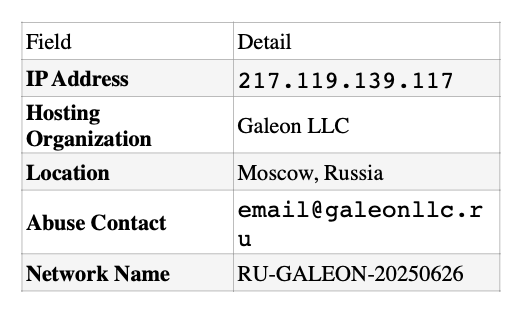
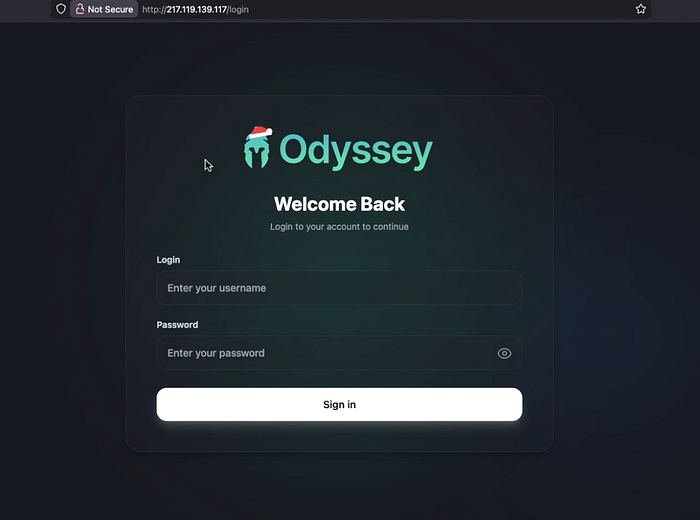
5. Admin Panel & Command & Control (C2) The AMOS variant is operated as Malware-as-a-Service (MaaS) via a web-based administrative panel.
- Panel Functionality: The panel allows the attacker (affiliate "xxxblyat") to manage infected bots, view stolen logs, and execute arbitrary shell commands via the persistent backdoor.
- Persistence Strategy: The malware installs a .plist file in the user's LaunchAgents directory, configured with the <key>KeepAlive</key> <true/> setting to ensure it restarts automatically after a reboot.
- Authentication Bypass: It uses a fake system prompt to steal the user's password, which
- is then verified using the dscl (Directory Service Command Line) utility to ensure the attacker has root-level access.
6. MITRE ATT&CK Mapping
7. Remediation & Incident Response
- Network Level: Block all traffic to 217.119.139.117 across the enterprise.
- Host Level: Scan for hidden files starting with . in the root of /Users/ [username]/.
- Credential Revocation: Critical. Treat every password stored in the browser as compromised. Force a logout on all active sessions (Google, O365, Exchanges).
- Crypto Safety: If the victim has used a software wallet, the Seed Phrase is compromised. Move funds to a new, hardware-generated wallet immediately.
8. Screenshot from analysis

This shows that this Campaign is Only for Mac users!

